Introduction
A good mystery should be a treasured find. Accompanying an investigator on their adventures as they try to undercover the truth or track down a criminal is an experience like no other, no matter what style of detective they are. Nothing works up adrenaline like accompanying a hard-hitting detective tracking down a murderer. Nothing excites the logical parts of the mind like seeing a skill sleuth unravel the convoluted trappings of a mastermind’s schemes. And nothing is quite as hilarious as watching a bumbling detective stumble through an investigation, cause mayhem, and still somehow end up solving the enigma. While it is hard to whittle off many of the great detectives that have been created for humanity by the minds of writers throughout the years, we have undertaken that difficult task and came up with 30 of the best fictional detectives in history.
In No Particular Order…

Picture courtesy of Flickr user dynamosquito
Sherlock Holmes – No list about the best fictional detectives will ever be complete without this infamous gentleman detective from the mind of Sir Author Conan Doyle. Detective Holmes has been the inspiration for many, many investigative characters since his birth in the late 1800s. He has been reimagined on stage, in radio shows, and quite a few movies. As a detective, he is known for his logical reasoning, early use of forensic science, and penchant for costume. Quote: “Elementary, my dear Watson” In truth, this was never uttered by our esteemed Holmes but it is nevertheless representative of the character and his attitude.

The Hardy Boys – Inspiring the adventures of young boys since 1927, Frank and Joe Hardy, the teenage brother detectives, have appeared continuously in print, have starred in computer games, television shows, and even been parodied in South Park. The earliest books were praised for the excellent writing of a caliber not normally found in children’s books of the era. Surrounded in a rather felonious small American town, they play perfectly bonded intelligent young men with free access to cash as they weave their way through the mystery and action that lands in their path. Quote: “A secret door!” Joe said. “We haven’t’ seen one of these in, oh, several months,” Frank said.

Nancy Drew – Much like theHardy Boys, Nancy Drew has been inspiring girls since the 30s. The character was even the brainchild of the Stratemeyer Syndicate, the same group responsible for the Hardy Boys. Nancy was an immediate hit and has seen continued popularity ever since. My like the Boys, she’s appeared in television, movies, and video games. She has been an inspiration for a number of other girl detectives, and kick started a genre all its own. She is well known for having a can-do attitude, especially noticeable in her ability to drive and fix up her own car. Despite attempts to keep her domesticated by generations of ghost writers, Nancy has managed to maintain her independent quality. Quote: “If a guy’s hunch results in a dead-end, don’t flaunt your better judgment and intuition in front of him. Smirk secretly to yourself.” – The Phantom of Pine Hill

Miss Marple – The brainchild of Agatha Christie, Jane Marple appeared in 12 novels and 20 short stories as an elderly spinster who fills up her free time resolving the assorted mysteries in her home of St. Mary Mead. She is the counterpart to the gentlemen detective genre, a well-bred, well-educated older woman applying her keen wit, experience, and knowledge to the challenges of solving crime. The character evolved markedly over 40 years, starting off as a shrill and nasty gossip and growing to a more dynamic and well-rounded genteel lady. She had a remarkable tendency to connect every case to a story of her past and casual comments to key details of her current case. Quote: “People with a grudge against the world are always dangerous. They seem to think life owes them something. I’ve known many an invalid who has suffered worse and been cut off from life much more… and they’ve managed to lead happy contented lives. It’s what’s in yourself that makes you happy or unhappy.” – A Murder is Announced

Dirk Gently– This fictional detective created by Douglas Adams was introduced in the books Dirk Gently’s Holisitc Detective Agency and the Long Dark Tea-Time of the Soul. His real name is Svlad Cjelli which, as Dirk puts it, has a ‘Scottish dagger feel’ to it. Known for his ‘holistic’ approach to investigations, Dirk uses this to justify his extensive bills which include things like tropical vacations. Surprisingly, none of his clients ever manage to actually pay him. He is also a psychic in denial, believing himself to have a ‘depressingly accurate knack for making wild assumptions.’ He was supposed to appear in a third book, The Salmon of Doubt: Hitchhiking the Galaxy One Last Time, but it was never completed. Quote: “Don’t you understand that we need to be childish in order to understand? Only a child sees things with perfect clarity, because it hasn’t developed all those filters which prevent us from seeing things that we don’t expect to see.” – Dirk Gently’s Holistic Detective Agency

Philip Marlowe – Arguably one of the most significant figures in the ‘hardboiled crime fiction’ genre, Marlowe was first created by Raymond Chandler in 1939 for The Big Sleep. He also appeared in Farewell, My Lovely, and The Long Goodbye. This was followed by a number of films, radio shows, television adaptations, and one videogame. Philip is the hard drinking, gruff yet oddly charming PI. His rough personality is rounded out with a thoughtful mind well versed in poetry, philosophy, and a fair hand at chess. He drinks whiskey and is finicky over his coffee. The femme fatales common to the genre aren’t nearly as adept at distracting him. Quote: “I don’t mind your showing me your legs. They’re very swell legs and it’s a pleasure to make their acquaintance. I don’t mind if you don’t like my manners. They’re pretty bad. I grieve over them during the long winter nights.” – The Big Sleep

Picture courtesy of Flickr user California Cthulhu (Will Hart)
Sam Spade – Though not as widely appearing as some of his peers on this list, Sam Spade nevertheless left an indelible mark upon the detective genre. Famously portrayed by Humphrey Bogart in one of the movie adaptations of his book, The Maltese Falcon, Sam Spade is not at all a gentlemen detective. He’s a shifty character capable of getting himself in and out of fixes with equal skill. Despite disliking his partner, even sleeping with the man’s wife, he goes all out when the man is murdered to bring his killers to justice. Quote: “The cheaper the crook, the gaudier the patter.” – The Maltese Falcon

Lord Peter Wimsey – Lord Wimsey is an archtypical representative of the British gentleman detective as conceived by Dorothy L. Sayers. He appeared first in Whose Body? In 1923 and subsequently solved murder mysteries in another 13 novels, 5 short stories, and assorted stage, television, film, and radio adaptations. In addition to solving assorted murders in his spare time, the great Lord Wimsey authors his own books, including ‘Notes on the Collecting of Incanabula’, his other genteel hobby. He is also a wine, fashion, and classical music aficionado. The character was in part a light satire on the British upper class. Quote: “It’s all right, Helen. That’s not swearing, that’s an adjective of quality.” – Clouds of Witness

Hercule Poirot– Around for a remarkable 55 years and appearing in 33 novels and over 50 short stories, Mr. Poirot has been a fixture in the detective genre for many years. Created by Agatha Christie alongside Miss Marple, this dignified Belgian detective solves crimes with the use of logical reasoning, or as he puts it ‘order and method’. Mr. Poirot also appeared on stage, in a number of film adaptations, several television shows, an animated series, and a number of radio dramas. Quote: “Chief Inspector, you have been thinking again. I have warned you of this before.” – Hercule Poirot’s Christmas (#6.1)

The Scooby Gang – The gang of animated teenaged friends (and one oversized dog) solve mysteries much to the dismay of the perpetrators whose plots they foil. These meddling kids include an unlikely array of friends, the All-American teen couple Daphne and Fred, the intelligent and shy Velma, the fumbling and perpetually starving Shaggy and his trusted sidekick and trouble-maker Scooby. These teens have a knack for shattering attempts to use fear of the supernatural to conceal criminal activity. Their antics inspired many television series, a number of films, video games, and stage performances. Quote: “Velma, here’s the only thing you ever need to know about boys. They are stupid. If you give a boy two choices, a smart one and a stupid one, he will always make the stupid one every time. That’s why you never give them a choice.” – Daphne Blake in Scooby-Do! Mystery Incorporated
Picture courtesy of Flickr user ostromentsky
Columbo – A homicide detective for the LAPD, Peter Falk is a gregarious, slightly rumpled detective who manages to get the job done in part because most of his targets underestimate him. He tends to talk too much and often seems to be a bit of an airhead, though in reality he has a keen attention to detail and a quick wit that helps him piece together the events of the crimes he investigates. The series ran for 10 seasons from 1972 till 1990 and continued in special runs as recently as 2003. Quote: “Perfect murder, sir? Oh, I’m sorry. There is no such thing as a perfect murder. That’s just an illusion.” – Columbo: Now You See Him (#5.5)

V.I. Warshawski – Warshawski is a woman in charge: sexy, smart, and packing heat. After earning a law degree and serving as a public defender, she decides to go the route of the one pursuing justice on the streets, particularly in the case of white-collar crimes that might not get as much attention from the police in the gritty world of Chicago politics. The fierce detective is not afraid to get into the melee, making it quite amusing that her best friend is the one who treats the war wounds from her escapades. Due to her ferocity and strength, Washawski is considered by many to be a strong, feminist detective. Quote: “Never underestimate a man’s ability to underestimate a woman.” – V.I. Warshawski

Dr. Temperance “Bones” Brennan – Based loosely on real life real life anthropologist and author, Kathy Reichs, Dr. Brennan represents a very unique sort of detective on this list. She solves crimes current and ancient with her companion FBI agent, Seeley Booth and a crew of brilliant and eccentric scientists housed at the Jeffersonian Institute on the TV show Bones. Her top-of-field expertise in forensic anthropology allows her to unravel clues from the bones of the victims. Her no-nonsense attitude and adherence to an absolutely logical worldview both aides in her field investigations, generating a lot of unintentional hilarity along the way. The character also applies her professional knowledge to her writing career, becoming a bestselling author of crime novels during the course of her show. Quote: “I’ve noticed that very few people are scary once they’ve been poked in the eye.” [to murderer who is trying to put a voodoo curse on her, so she pokes him in the eye to shut him up] – “Bones: The Man in the Morgue (#1.9)

Perry Mason – Mason is one of the most famous and prolific figures in recent detective fiction. Featured in close to 100 novels, a radio series, two television series, and over 30 made-for-TV movies. As a defense attorney, he was known for not shying away from the most difficult and hopeless cases and always fighting to the end for his clients. He does engage in some questionable actions early on in his history, but for the majority of his existence, Mason is an ethical idealist who sticks to the books and wins his cases by his wits and the evidence. The Mason stories do conform to a predictable pattern, but the enjoyment is in the details. Quote: “She’s more of a legitimate fake than I thought she was.” – The Case of the Curious Bride

Elijah Baley– Though he does not appear in a large number of works, Baley’s impact on the world Isaac Asimov created is profound. There are only four stories that feature Baley: The Caves of Steel, The Naked Sun, Robots of Dawn, and a short story titled Mirror Image. He operates in a world far different from ours, where robots are commonplace and Earth is filled with humans who live in enclosed cities. The mysteries Baley investigates are worthwhile for their whodunit quality, but they also investigate questions of a sci-fi nature and connect to the greater works of Asimov. Quote: ““The work of each individual contributes to a totality and so becomes an undying part of the totality. That totality of human lives–past and present and to come–forms a tapestry that has been in existence now for many tens of thousands of years and has been growing more elaborate and, on the whole, more beautiful in all that time. Even the Spacers are an offshoot of the tapestry and they, too, add to the elaborateness and beauty of the pattern. An individual life is one thread in the tapestry and what is one thread compared to the whole?” – Robots and Empire

Harry Dresden – Part detective, part fireball-throwing wizard, Harry Dresden has the unenviable task of solving mysteries in a world where things do not always conform to the rules of nature and science. The Dresden Files, the name for the book series and the short-lived television series, follows Harry through a world of vampires, werewolves, spirits, and crimes both mystical and mundane. Harry himself is a tough, stubborn young man with a sharp wit he used for detective work and pithy remarks against antagonists. Did we mention he can shoot fireballs? Quote: “Laugh whenever you can. Keeps you from killing yourself when things are bad. That and vodka.” – Changes

Kinsey Millhone – The main character in Sue Grafton’s alphabetically named series of detective stories, Kinsey Millhone is a feisty woman who has never quite played by anyone’s rules but her own. She was a delinquent as a teenager, dropped out of academics to pursue police work for more action, became an insurance investigator after that proved boring, and finally went on to become a private detective. The books are well-written murder mysteries that pit Millhone into tough situations only to prove she is tougher and smarter than anything that comes her way. Quote: “You can’t save others from themselves because those who make a perpetual muddle of their lives don’t appreciate your interfering with the drama they’ve created. They want your poor-sweet-baby sympathy, but they don’t want to change.” – T is for Trespass

Photo courtesy of Flickr user cdrummbks
Dave Robicheaux – James Lee Burke’s bad boy detective patrols the swamps of New Iberia, Louisiana, managing to break most of the rules, fight off his inner demons, and still catches the criminals at the end of the day. Some readers may find Robicheaux an overly cynical and irritable antihero, but the character is rounded underneath the wooden exterior. The murder and mayhem in the books is as gritty and dark as Dave, setting the stage for an enjoyably gruesome world of murder mystery. Quote: “When people make a contract with the devil and give him an air-conditioned office to work in, he doesn’t go back home easily.” — In the Electric Mist With Confederate Dead

Photo courtesy of Flickr user Jeffrey Beall.
Charlie Parker – It is difficult enough to be a detective, and dealing with supernatural horrors at the same time makes it a true challenge. John Connolly’s underappreciated work is a wonderful world to dive into for those looking for a more obscure detective series. Parker himself is a bad boy in a bad world, and Connolly masterfully blends the touch of supernatural horror alongside the shadow of mystery. The horror and supernatural elements do come to take on a greater focus as the series progresses, so if you are looking for a realistic detective series, the Charlie Parker series may not be the best bet. Quote: “Why did you shoot him?” “You weren’t around,” I replied, my teeth gritted in pain. “If you’d been here I’d have shot you instead.” – Every Dead Thing

Image courteys of Flickr user scampion
Harry Bosch – Hieronymus Bosch, called Harry by most, had a rough time as he grew up. He was born to a prostitute, did not know his father until much later, his mother died when he was 11, he bounced between foster homes, and ended up in Vietnam while still a teenager. Despite the fires Michael Connelly put his detective through, Bosch turns out to be an all-around good guy who believes in doing the right thing, even if it means going against the norm or the boss. If you find yourself making it through all 16 Bosch novels and still wanting more, check out Connelly’s Mickey Haller series. Quote: “Everybody counts or nobody counts.” – Personal motto of Harry Bosch.

Bobby Goren – A main character in the Law and Order spinoff Criminal Intent, Goren is a dogged investigator with an attitude and a sometimes violent temper. His passion for justice is the main cause of his occasional rages, but there is no questioning that he gets the job done, even if criminals have to be wary of him for more than just the high likelihood of him putting them in chains. Law and Order stories are always gripping, and Bobby Goren is one of our favorite lead investigators throughout all of the spinoffs for blending humor and skill while being vulnerable enough in his emotional issues to be relatable. Quote: “The only medical condition you have is denial.” – Law & Order: Criminal Intent: Jones (#1.5)

Batman – The Dark Kinght might seem to be a poor example of a detective if you were to base your opinion off just the recent movies starring Christian Bale, but the real Batman does just as much investigation as he does bad-guy stomping. Armed with the latest in technology for whatever era he is in at the time, photographic memory, and sharp analytical skills, Bruce Wayne is the only one who can root out the hidden plots of the nefarious super criminals in Gotham City. Of course, once he does find out what they are up to, he puts the fear of the bat into them. Between multiple comic book series, cartoons, live action shows, movies, and games, you will have trouble getting through all of the available material on Batman without devoting time to him every day. Quote: “He thinks he can scare me. He thinks he can stop me. There’s nothing wrong with him a bullet in the head won’t fix.” – Batman Detective Comics Vol 1 734, Mark of Cain:2

Dick Tracy – The world of Dick Tracy is a dark one inspired by the feel of Chicago in the 1930s, full of grotesque and cruel villains, backstabbing, and the hopelessness of the fight against crime. You can draw many parallels between Batman and Dick Tracy: both are detectives, fancy gadgetry becomes important later on in the Tracy series, and both have cities plagued by demented criminals. Tracy is the less skilled detective, though that could be due to his cases being relatively simple, but he has the everyman spirit that billionaire Wayne can never have. Quote: Breathless Mahoney: “Thanks for calling. I was beginning to wonder what a girl had to do to get arrested.” Dick Tracy: “Wearing that dress is a step in the right direction.” – Dick Tracy (1990)

Dr. R. Quincy, M.E. – One of the first shows to include hard forensic science, Quincy M.E. follows the work of forensic pathologist R. Quincy, whose first name was never clearly given. A gentleman and a scholar, Quincy uses his position as a medical examiner to probe into their deaths and root out the real killer. Later on in the series, he even finds himself in the middle of deep social issues of the time. If you want a taste of the original version of CSI, check out Quincy M.E. Quote: “Gentlemen, you are about to enter the most important and fascinating sphere of police work: the world of forensic medicine, where untold victims of many homicides will reach back from the grave and point back a finger accusingly at their assailant.” – Quincy M.E.: Go Fight City Hall… to the Death (#1.1)

Lennie Briscoe – A major character in the Law and Order universe, Briscoe was the head detective in the original series and had appearances in both the Trial by Jury and Special Victims Unit spinoffs. His quips at the crime scene, sharp one-liners, cool demeanor, and dry wit belie his dedication to his work and getting to the truth. The best part about getting to know Briscoe is that you have almost 300 episodes in which to do it. You will also likely come to enjoy Briscoe’s interactions with his two partners: the stodgy and moral Curtis, and the brash rule-bender Green. Quote: “Love: a devastating disease instantly cured by marriage.” – Law & Order: Couples (#13.23)

Inspector Gadget – Another on our list who began as a cartoon, Inspector Gadget could be considered a defective detective, reminiscent of other simpleton detectives like our next one. Luckily, being a cyborg full of interesting tools like a helicopter, spring-loaded feet, and other crime-fighting tools keeps him going in the crazy situations in which he puts himself, and the crimes always end up being solved thanks to the work of his daughter, Penny, and their intelligent and aptly named dog, Brain. Quote: “It’s like I always say, Penny: If you can’t lick ’em, join ’em. Then lick ’em.” – Inspector Gadget, Down on the Farm
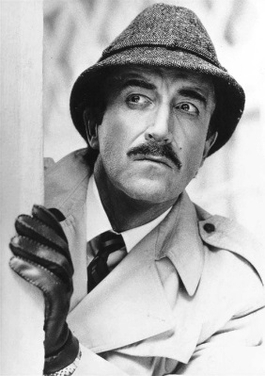
Inspector Clouseau– Proving that you do not have to be smart to be a successful detective, at least in the world of fiction, Clouseau is the epitome of the bumbling detective archetype. Even the above detective’s outfit was based on Clouseau’s typical attire, as homage to the older compatriot. Despite Clouseau failing at even the most basic investigative tasks in dramatic fashion, he always seems to come out ahead and solve the case. His unlikely successes are so far beyond the realm of reason that they even drive other characters in the story insane. To catch the first appearance of Inspector Clouseau, watch the original The Pink Panther from 1963. Quote: ”There is a time to laugh and a time not to laugh, and this is not one of them.” – Inspector Clouseau (1968)

Adrian Monk – Portrayed by actor Tony Shalhoub, Adrian Monk is a neurotic mess. Once a successful detective, the death of his wife due to a car bomb possibly intended for him exacerbated his obsessive compulsive disorder and various phobias to the point that he could no longer function on the force. Eventually, his keen powers of observation and great detective work get him pulled back in as a consultant, though his issues make every adventure even more challenging than it is for a saner person. The show and Shalhoub have won multiple awards, and there are several connected books if you finish the series and crave more. Quote: Sharona Fleming: “Are you sure you’re not getting your hopes up?” Adrian Monk: “That’s what hopes are for.” – Monk: Mr. Monk Goes to the Carnival (#1.5)

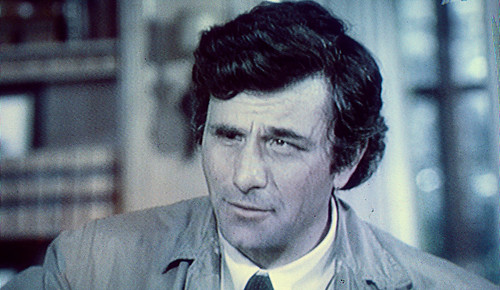
Spencer is pictured sitting in the front and center.
Shawn Spencer – Spencer is the lead character in the television series Psych. A child at heart, Shawn never professionally studied how to be a detective, instead learning the powers of observation – to the level of an almost photographic memory – and deduction from his detective father. After a string of failed jobs as an adult and with no credibility to his name, he does what any would-be detective would do: pass off his heightened awareness as extra sensory perception. Accompanied by his best friend, a pharmaceutical salesman named Burton Guster, Shawn begins to solve cases for the Santa Barbara PD while maintaining a façade of supernatural power, delivering pithy humor, childish antics, and daredevil actions. While his appearance is limited to the show, he is still one of the best and most entertaining detectives you will find. Quote – “Oh, you mean my pilot’s license? That’s out back in the Cessna. Or perhaps you’re referring to my license to kill. Revoked. Trouble at the Kazakhstan border. I could give you the details but then I’d have to kill you, which I can’t do because my license to kill has been revoked.” – Psyched: Poker? I Barely Know Her!

Magnum P.I. – Despite being somehow down and out regardless of a string of private cases, Magnum lives one of the most lavish lifestyles of any detective on the list. Set in the scenic Hawaii and in the same fictional universe as Hawaii Five-0, Thomas Magnum is equipped with a number of useful tools: a helicopter pilot friend, an amazing sports car, a glorious mustache, and the best Hawaiian shirts available. He is also notable for being one of the first depictions of a Vietnam veteran. With beautiful women, interesting cases, and tons of action, Magnum P.I. should be on the short list for anyone looking for a detective series to watch. Quote: ”I’m not really sure which kind of private investigator I am. The Holmesian-type with the constant deductive mind, or one with a Marlowe-type intuitive sense of the darker side of human nature? Hopefully a combination of both. At any rate, it doesn’t matter. Not when you have a “little voice”. I don’t know, maybe a gently nagging “little voice” is just another way of adding what you know, to what you feel, but right now mine wasn’t “gently nagging”. It was screaming.” (Narration) Magnum P.I., Round and Around (#6.6)