The wrong reputation
Summer is technically over on the Autumn Solstice (between the 21st and 24th of September) but for many, Labor Day (September 4th) heralds the beginning of the end, causing many to view it through a bittersweet lens. Many forget that Labor Day was not created to signal the end of a season, it was meant to signal the end of worker oppression.
Labor Day honors the long and toiled history of labor in the United States. Before the 8-hour workday, people typically worked 10 to 16 hour days, 6 days a week and -- despite laws being passed -- endured years of poor working conditions and strikes for their rights. Labor Day recognizes the strength and appreciation of the American workforce.
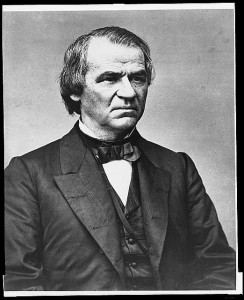
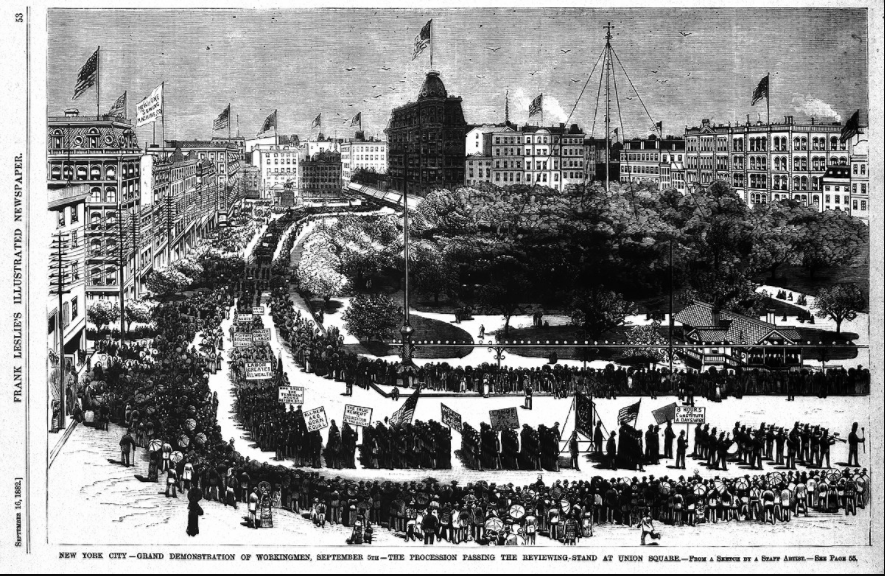
In an effort to spur and support worker’s rights, the first Labor Day celebration was held on September 5, 1882. In 1887, the first state to make Labor Day a holiday was Oregon, with New Jersey, New York, and Colorado following suit. In 1894, after public outcry over the death of workers during the Pullman Strike, President Grover Cleveland made it a national holiday and a symbol of the Labor Movement.
The wrong representative?
There’s still debate over who actually founded Labor Day: Peter J. McGuire (the man with the plan) or Matthew Maguire (the man who acted on the plan).
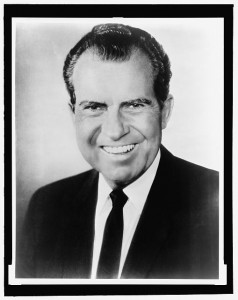
Peter J. McGuire was the founder of the United Brotherhood of Carpenters and co-founder of the American Federation of Labor (AFL). He led a series of strikes that led to the enforcement of the 8-hour workday law (originally passed in 1868, by the way). On a trip to Toronto, he observed a Canadian Labor Day celebration where 1/10 of the population of Toronto marched for unions and better labor laws. Inspired, he suggested that the Central Labor Union of New York do the same.
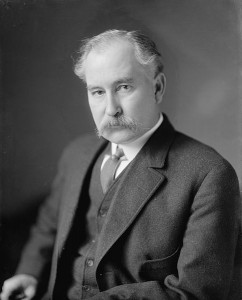
Working as Secretary of the Central Labor Union of New York, Matthew Maguire (note the different spelling of the last name) organized that very first Labor Day parade. A machinist and radical figure in the Socialist Labor Party of America, he also led strikes in the 1870s against working conditions and long hours.
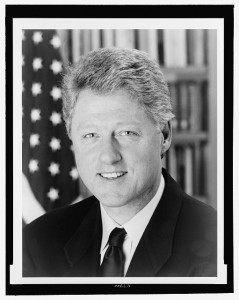
Whether a conflict of interest or an interest in avoiding conflict, Samuel Gompers, co-founder of the American Federation of Labor, gave the “founder” title to his other co-founder, Peter J. McGuire.
Regardless, wrong finally goes right
The early hours of the first Labor Day parade saw low attendance due to worried workers losing money - or their jobs. However, it’s said that once the band started playing, an estimated 10,000 to 20,000 people showed up. After the parade ended, some went back to work while others continued the celebration in Wendel’s Elm Park. The party lasted until 9 p.m. and included food, speeches, and a lot of beer.
Parades were the common way to celebrate holidays and were typically followed by festivals around town - after parties if you will. The Labor Day festivals eventually grew so big that they became hard to maintain. To solidify the meaning or simply maintain order, organizers began to focus less on beer and more on speeches about the economic and political significance of worker achievements. Labor Sunday was also established to focus on the spiritual and economic achievements of the Workers Movement.
The beginning of the end
Through the past century, Labor Day has seemed to achieve the opposite of its intended effect. Relaxation has become rushed and an “enjoy it while you can” mindset has taken over (perhaps that mindset was always there, but for a different reason).
- Many take their vacation days to have one last getaway with family before the school year begins.
- Less summer means less time off, and so amusement parks and other harbingers of fun close after Labor Day.
- Somehow Labor Day signifies when people switch to their fall and winter clothes, so hurry up and wear out the white.
- Fall’s favorite sport, NCAA football, holds its first games during Labor Day weekend, the NFL the weekend after.
- Recently, Labor Day has become an important weekend for end-of-summer and back-to-school sales - the ultimate rush.
Although the way Labor Day is celebrated has changed, it’s important to take the time to remember and appreciate the fact that we don’t work 12-hour days and have better working conditions, so enjoy that day of rest before it’s back to being “busy.”

 EMBED THIS INFOGRAPHIC ON YOUR SITE
EMBED THIS INFOGRAPHIC ON YOUR SITE EMBED THIS INFOGRAPHIC ON YOUR SITE
EMBED THIS INFOGRAPHIC ON YOUR SITE