The 20 Worst Data Breaches
The information technology age has brought with it a new opportunity for the criminally minded. Unfortunately, our government agencies and corporations have not always been as guarded as they could be against those determined to gain access to the vital data they store. Through a combination of hacking and social engineering techniques, digital thieves have made off with identity information, hampered affairs of state, and even stolen millions of dollars. Here are 20 of some of the most damaging, notorious, or notable data breaches presented in chronological order.
- Card Systems – 2005
Card Systems is a third-party processor of credit card information based in Tuscon, AZ. In June of 2010, a hacker slipped a data-mining bug into their system through security holes and stole data over time from roughly 40 million cards. This data breach happened in large part because the company was storing cardholder’s account numbers and their security codes, in direct violation of MasterCard rules, which allowed the hacker to collect it. The information gathered was suitable only to steal money from the credit holder’s accounts, not to steal identities. At the time, it was the largest data breach to date.

In 2006, burglars broke into the home of a VA employee who had taken his company laptop home, in violation of that agency’s regulations. Fortunately, the thieves responsible for stealing the laptop in question had no idea what they had gotten their hands on and deleted all the relevant information. When FBI agents recovered the laptop, they found it had been cleared and reformatted for quick resale, thus protecting the millions of veterans whose information had been stored. The data in question included Social Security numbers, names, addresses, and birthdays for millions of veterans, current service members, reservists, and their spouses. It did represent the largest data breach from a government agency in US history, and raised a lot of questions about how we enforce and protect the highly sensitive data government employees have access to.

<
- TJX Companies Inc – 2007
TJX Companies is a large retailer that includes a number of retail chains like HomeGoods, Marshalls, T.J. Max, and others. Over the course of several years, predominantly in 2003 and 2006, an unknown number of hackers made stole millions of transaction data. Of note, it took TJX over two months after the data breach was discovered to talk about the true size and scope of what occurred with the media, and even delayed discussing their awareness of it with affected banks and customers. In the end, 45.6 million card numbers were stolen and data from over 450,000 merchandise return receipts were also taken. This represented another major wake-up call for the industry. It took TJX seven months after the theft to recognize it, and retracing the hacker’s steps proved challenging since they lost much of the trail in normal data purges.

- TD AmeriTrade – 2007
Once again, a company with a major data leak chooses to withhold this information to its customers for half a year before disclosing it. In this case, AmeriTrade was made aware at least as early as October of 2006 when customers began to complain of stock-related spam emails. That led to a lawsuit in May of 2007 when two of its customers actually sued the company for the breach. Each client had an email addressed used exclusively with TD AmeriTrade and when those inboxes began to fill up with unwanted ads, they immediately knew where the leak had come. The problem was even noted on BoingBoing in June of that same year, when they featured a review of AmeriTrade which noted similar email spam to their dedicated address. Despite this, the company kept the information close to the chest until September when a court order would have forced them to step forward anyway. The lawsuit suggested that the data breach could have potentially leaked sensitive customer data like Social Security numbers and other information that could be used in identity theft. There was also a concern that the company might attempt to destroy information that would display their negligence. The company then requested a two week break from court proceedings, was granted it, and used that time frame to ‘discover’ the breach and notify the press and their clients. It became very clear that they choose to respond not out of a sense of responsibility to their clientele, but purely because they’d been caught and could no longer contain the story.

- Certegy – 2007
This case was pretty much a cut-and-dry case of more traditional data theft – a disgruntled employee sold information to a data broker. The details that make this case worth examining is how the company presented the scope of the problem initially and how they recovered. They claimed after it happened that only 2.3 million records were stolen and that the public should not be concerned, because these records were all going to ‘legitimate marketing firms.’ A few months later it was revealed through a filing with the Securities and Exchange Commission that the true number of stolen records was in the range of 8.5 million. Of those records, roughly 5.7 million included checking account records, and 1.5 million included credit card records that could be used for identity theft and fraud. In the end through a settlement with the Florida Attorney General, consumers were granted a two year period to report and receive reimbursement for expenses related to theft from the incident, and they were given credit monitoring at the company’s expense. Further, the company restructured how it handled information security, doing a comprehensive review of internal and external risk, implementing a range of safeguards, and scheduling regular tests and monitoring programs to detect weaknesses and catch issues before they became problems.
- Monster – 2007
Monster actually had a recurring problem with data breaches between 2007 and 2009. Three separate times they suffered data breaches in which millions of customer’s personal data was stolen or had their job listings infected with malware. Users affected also saw targeted phishing emails encouraging them to download malicious software or tempting them to accept jobs working as mules for online criminal organizations. One of the malicious Trojans left behind by the attacker’s encrypted files on the affected user’s computer and left a text file demanding payment to the attackers to recover the data. Each attack was perpetrated by hackers abusing security weaknesses in their information security structure. Each time, Monster delayed informing its users that there was a breach after becoming aware of it. Each time, Monster swore to do better. Unfortunately, as Monster learned, big talk is not enough to deter hackers. Actual improvements in infrastructure actually have to be accomplished, not just discussed.

- Bank of New York Mellow – 2008
Another case of traditional theft leading to a massive data leak, Bank of New York Mellon discovered a missing box of data storage tapes in February and again in April of 2008. Each time, these tapes were being transported by third party vendors from one location to another when they went missing. Surprisingly, these tapes containing vital customer information were not at all encrypted. In addition, the bank did not inform potentially affected customers for three months. Initially, the breach was believed to have affected over 4 million individuals and included names, addresses, and Social Security numbers. Later that year, the bank notified 12 and a half million customers that their data had been stolen. All affected customers were offered two years of free credit monitoring and identity theft insurance worth up to $25,000.

- CheckFree – 2008
At the time of the attack, CheckFree was the largest e-bill payment system on the internet, controlling between 70-80% of the US online bill pay market. This made it a prime target for smart hackers. For several hours, hackers managed to redirect visitors from the legitimate site login page to a site based in Ukraine that attempted to install software designed to steal customer’s passwords. CheckFree at the time had more than 24 million users, so the attack had the potential to be devastatingly effective. This attack was not due to a problematic infrastructure on CheckFree’s part. The hackers had legitimate codes to access CheckFree’s website, suggesting they either successfully phished that information from a CheckFree employee or utilized password-stealing malware. This same website in Ukraine attacked at least 71 other domains at the same time. The attack was noticed and responded to promptly by CheckFree, who had plugged the leak the same day. They promptly informed their customer base, instructed them how to detect malware infection, and arranged for every affected customer to receive a free copy of VirusScan Plus from McAfee.

- Hotmail – 2009
In another phishing scam, about 10,000 Hotmail users had their passwords stolen. Much like the CheckFree incident, users were redirected to a site resembling the Windows Live Hotmail login screen. Users who were fooled into entering in their password and user account found their information later posted on Pastebin.com, a site originally designed to allow web developers to easily share tidbits of code. This same site had a list of over 30,000 Gmail, Yahoo! Mail, AOL, Comcast, and Earthlink email accounts and passwords. Microsoft responded quickly upon learning of the breach, sending out emails to warn affected customers of the potential problem and forcing password resets on all affected accounts. As with CheckFree, this was not a failure of Hotmail’s own data security, but a successful phishing venture.
- Heartland Payment Systems – 2009
Thought to be the largest data breach of a payment processor, the 2008 attack of Heartland Payment Systems affected roughly 130 million customers and raised a few questions about the effectiveness of PCI standards of the time. The CEO Robert Carr adamantly reported that Heartland was in full compliance with PCI standards and was certified as such. The PCI Security Council contested his claims, suggesting that the breach was a result of an SQL injection error. Even still, the company was certified as fully compliant, leading many to conclude that companies should go beyond the basic requirements of PCI to protect customer data. Particularly with regards to tracking security standards over time, as errors creep into systems and hackers gain more sophisticated tools. Heartland developed an E3 end-to-end encryption service to monitor and secure the whole payment process from point-of-sale all the way through authorization and approval. The PCI Security council also began looking into technologies like card tokenization to improve their own standards. The end result was more focus on a layered approach to information security. In the end, Heartland paid more than $110 million to Visa, MasterCard, American Express, and other card companies to settle claims related to the breach, customers were notified and offered credit monitoring, and companies gained a sobering check about the state of their data security.
Once again, the VA put data from roughly 76 million veterans at risk through employee negligence. In this case, the breach started with a faulty hard drive in a database RAID array. Employees arranged for a contractor to repair the disc and neglected to erase the encrypted data stored on the disc. When the contractor failed to repair it, the disc was recycled, leaving the data accessible to whoever next claimed the disc.

- Hannaford Bros. Chain – 2009
Much like Heartland, Hannaford Bros. supermarket chain appeared to be following PCI compliance standards when they were hit with a massive data breach. Despite their compliance, a sophisticated hacking attack exposed over 4 million credit and debit card numbers to potential identity theft risk, and resulted in almost two thousand cases of fraud. Later that year, Albert “Segvec” Gonzalez was indicted by a federal grand jury in New Jersey, along with two co-conspirators, on charges of hacking into Hannaford Brothers, Heartland Payment Systems, 7-Eleven, T.J. Maxx, and other unnamed national retailers. This individual and his small team were accused of stealing over 130 million credit and debit card numbers, the biggest fraud case of its kind in history. He was eventually sentenced to 20 years in federal prison for his crimes.

- VeriSign – 2010
The VeriSign attack was notable both for the severity of potential complications such a breach could have caused, and for the astounding lack of communication happening within the company. The data breach was first discovered by their security team in 2010, but this was not reported at all to management until September of 2011. An SEC filing made public the data breach, forcing the company to acknowledge the situation, though initially the upper level management seemed to have little knowledge of the incident beyond what was included in the filing. At the time of the attack, VeriSign was one of the largest providers of SSL certificates, which browsers use to identify secure sites like financial sites and communication portals. VeriSign also housed sensitive information on customers and the registry service used to create website addresses also a potential target. The big fear was that the certificate system was compromised; this would have allowed hackers to forge certificates (an event that had already occurred) and thus trick users into believing a phishing site was completely legitimate. Stewart Baker, former assistant secretary of the Department of Homeland Security responded to the event by saying, “Oh my God. That could allow people to imitate almost any company on the Net.”
- Gawker Media – 2010
Gawker Media’s security breach was a lesson in humility, the internet’s version of being publicly tarred and feathered. A feud between online message board 4Chan and Gawker (who is responsible for Kotaku, Gizmodo, Jezebel, Jalopnik, Lifehacker, Deadspin, Fleshbot, and io9) developed as the web publisher trashed 4chan’s antics. This was swiftly followed by denial-of-service attacks perpetrated by 4chan members. Shortly thereafter, a group with loose affiliation to 4chan who called themselves Gnosis began to infiltrate the Gawker’s content management system, internal communications systems, and user databases. There they sat for a period of time, during which Gawker’s founder was notified that his account was logged into their internal system when he was not. He ordered the account shut off, but did not bother to change his password. In a stunning display of stupidity, it turned out that he used the same password for everything. After playing around internally for a bit, Gnosis began to get public. They posted a snarky message via Gawker’s Twitter account suggesting that user accounts might be compromised. When a Gawker employee assured people that their information was safe, Gnosis responded by posting a meme and a message on Gawker’s site directing people to a Pirate Bay torrent containing a massive data dump that included internal conversations, user names and passwords for a number of employees and many site commenters, FTB account access, and the source code for their content management system (allowing hackers to dig through for weakness). It also revealed that they were three years out of date on their server’s security patches, were using horrendously out of date encryption on user passwords, and had zero protocol established for password creation; nearly 2,000 Gawker users has ‘password’ as their password. Gawker’s response was incredibly poor. Not only did Neck Denton, the founder, fail to respond in a sensible manner after being originally made aware of the problem, they then refused to admit that there was a problem because their passwords were ‘encrypted’ and then waited over a day before notifying users there was a breach. When they did notify customers, it was done with a message on their site, not via email, ensuring many users would never know there was an issue.

- ESTsoft – 2011
ESTsoft is a general purpose software company operating in South Korea. In 2011, they were the target of a devastating attack that impacted nearly the entirety of South Korea’s population. Hackers gained access to one of ESTsoft’s update servers and loaded malware that attached itself to their ALZip compression application, which subsequently infected 62 computers at SK Communications that made use of the ESTsoft program. The infected computers were then able to steal complete customer databases including addresses, contact information, passwords, and gender of roughly 35 million individuals in a nation with a total population of 49 million. The company apologized, the primary web portal for Korea, NHN, ordered employees to delete ESTsoft programs, and lawsuits were filed. The company never disclosed the financial cost of the breach.

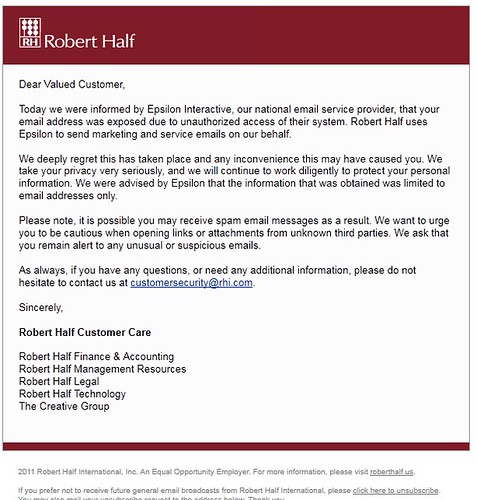
- Epsilon – 2011
In one of the largest data breaches of its kind, Epsilon was hacked in March of 2011. Epsilon handles over 40 billion emails annually and services more than 2,200 clients around the world. The information stored was primarily email addresses and names, including those of customers who had opted-out of marketing mailers, opening up all of those customers to phishing attempts. In addition, some users member points were accessed, giving thieves an upper hand when creating believable scam emails. Included in the many companies that sent out warnings to their clientele were major retailers, financial companies, cellular phone companies, banking institutions, and more. Roughly 3% of Epsilon’s clientele was effected. The Secret Service investigated the breach which is estimated to potentially cost Epsilon up to $225 million in damages.
- RSA Security – 2011
SecurID tokens, used in a two-factor authentication system which is designed to create a layered and stronger security system, were compromised in March of 2011 when RSA Security was hacked. Initially, RSA claimed that the hack would in no way allow any “direct attack” on the tokens. Then a few months later, the defense contractor Lockheed Martin fended off a hacking attempt in which the tokens failed to offer any layer of protection. In June RSA released a statement acknowledging the failure. Their Chairman, Art Coviello, claimed that the reason it took them 3 months to disclose the full scope of the breach was to protect other customers from attacks similar to what Lockheed Martin experienced. There were claims that Northrop Grumman and L-3 Communications faced similar attacks. The delay caused many to question the reliability of RSA’s system and certainly to worry that withholding that information put their customers at risk. Some choose to switch to a new token provider, but many remained with RSA because the cost of switching was much more expensive and time intensive than simply gaining new tokens (which RSA provided). In a rather ballsy gesture, RSA encouraged its customer base to increase the layers of RSA security to create redundancy layers. One product fails, so we’ll switch that one out and sell you two more.

- PlayStation Network – 2011
Some 77 million user accounts on Sony’s PlayStation Network were compromised after a large scale hack accessed the Sony database. It took the company seven days to notify their customers that data was stolen during the breach that caused their massive shutdown. Names, email addresses, passwords, security questions, birth dates, and addresses were accessed, and Sony warned customers that credit and debit card information may also have been stolen, though no cases of identity theft or fraud were reported as a result. The company was fined £250,000 (approximately $400,000 USD) by Information Commissioner’s Office, a UK based watchdog group, naming the clear negligence on Sony’s part as the reason for the fine.

- Bitcoinica – 2012
Bitcoin offered the internet world a unique form of new currency. The nature of Bitcoins makes it an irresistible target for hackers, as a key feature is the permanency of the peer-to-peer transaction style. While it protects merchants from chargebacks, it also means that a successful theft of the currency is one that cannot be reversed. Once a hacker gains access to the private keys, what they steal is theirs to keep. Bitcoin has see a lot of growth in recent years as it has become a haven for both criminal activity and as a sort of virtual stock market. It has also seen a rash of hacking attacks targeting trading platforms like Bitcoinia, who lost $87,000 worth of currency in an attack against their production servers and BitFloor, the largest Bitcoin exchange in the US, who lost $250,000 in a successful hack against an unencrypted storage server. Bt Gox, Instawallet, and other Bitcoin-supporting companies have also seen successful thefts. These thefts have considerably increased the risk of investment in Bitcoins, stalling what had been a dramatic growth in value in 2012.

- Global Payments – 2012
With a pricetag of $92.7 million in damages, investigation costs, lost business, and remediation expenses, the Global Payments data breach put at risk more than 7 million card numbers. The data that was stolen in the breach included full Track 1 and Track 2 data, usable by thieves to counterfeit new cards. Union Savings Bank was just one among a number of financial institutions affected by exactly that tactic. In March of 2012, thieves began purchasing small denomination Safeway-branded prepaid debit cards. They would then encode Union Savings Bank issued debit card accounts to the magnetic strip on these cards, use them to purchase high value prepaid cards, and spend the money buying high ticket electronics and other items from other retailers. USB alone suffered roughly $85,000 in expenses related to the theft. Some, like Fulton Bank of New Jersey were harder hit, seeing roughly one thousand stolen accounts every week. Visa and MasterCard promptly revoked their certification of Global Payments. Javelin estimated that $707 million in fraudulent charges will occur to the 1.5 million cards that were known to be compromised, with an end cost to consumers of roughly $152 million.

