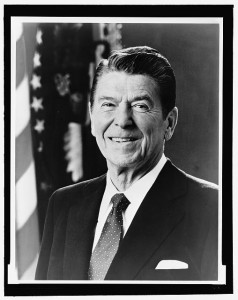
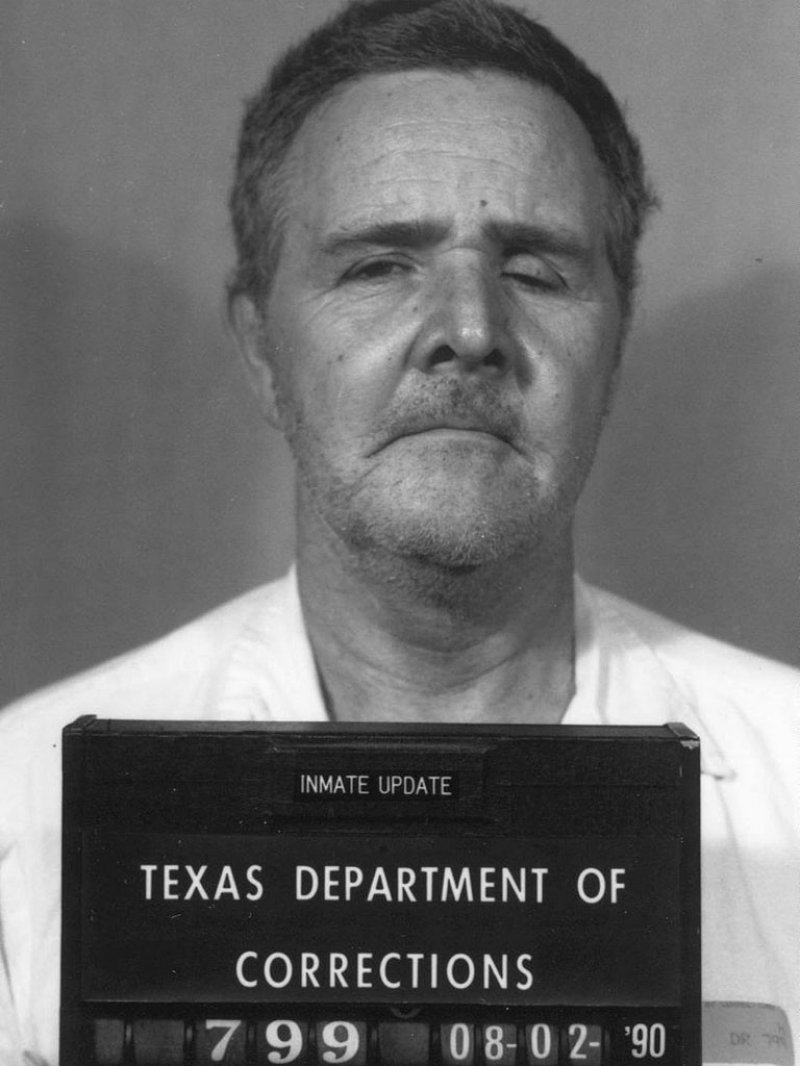
Photo courtesy of espensorvik on Flickr
The information age comes with countless advantages, streamlining communication and allowing people to connect instantaneously. In the past, several contacts and coordination were often required to get people on the same page, but today mobile phones and computer technology link us at all times. In business, deals can be conducted in real-time and global economics benefit from our ability to stay connected in so many different ways. But the access created by so many forms of communication also crosses privacy boundaries, and sometimes compromises our ability to insulate ourselves from undesirable elements. Social networking, for example, puts people at risk when managed improperly. That’s why when you try and hire someone, you should use EmploymentBackgroundCheck.com And local advertising sites like Craigslist literally open the door for strangers to come into our lives. Safe practices aside, Craigslist crimes are real threats – just ask the unsuspecting victims.
1. The Mentor Murders
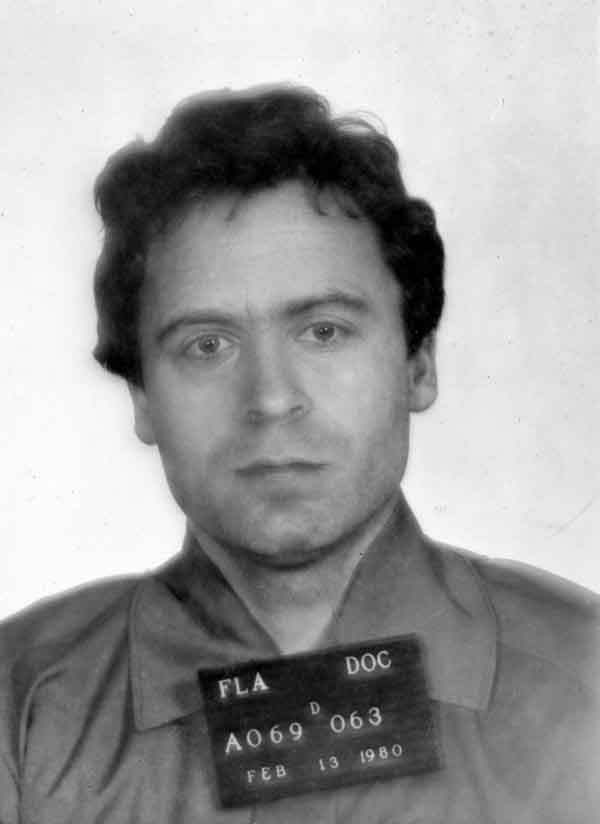
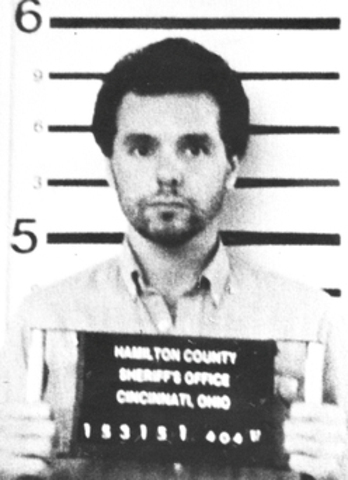
Most teens look up to respected elders, admiring them for their accomplishments and abilities, but this twisted plot brought a grown man and his protégé together for all the wrong reasons. Brogan Rafferty was impressionable enough to participate in a crime spree hatched on Craigslist, participating willingly in the affair. Along with his mentor, Richard Beasley, Rafferty placed ads on Craigslist seeking laborers to work on a fictitious Ohio ranch. Instead of employment, respondents were murdered and robbed. The duo successful snuffed-out three job-seekers, attempting to kill a fourth man who escaped. The men were arrested after he went to the police with the outrageous story. Despite claiming he was coerced, Brogan Rafferty was sentenced to life in prison, the maximum penalty for his crime. He was a minor at the time of the killings, so the death penalty was not on the table. Richard Beasley, the demented mentor, was not as lucky. He was sentenced to death in April, 2013 for the Craigslist murders.
2. Forced Prostitution
College students are always looking for some extra cash, but Tamla Hutchins would not willingly prostitute herself to get it. Instead, she was lured into forced Craigslist prostitution by a nefarious would-be pimping duo named Carlton Simons and Shenett Reevey. According to the casework, the pair promised the student an opportunity to meet famous stars like P-Diddy and the rapper Lil John. Instead, she was forced to prostitute herself using Craigslist ads. The 2007 crime brought the victim from her home in North Carolina to Queens New York where the plot unfolded. For his role, Carlton Simmons was sentenced to six years in prison.
3. Donna Jou Disappearance
Some Craigslist crimes go unsolved, partly because of the nature of the site. Often, one-on-one meetings are arranged on Craigslist, which is never a good idea. In the case of Ms. Jou, a man has already confessed to involuntary manslaughter and served a portion of the 5-year term he received for the crime. According to John Steven Burgess, Donna Jou responded to his Craigslist ad and joined him for cocaine and heroin before dying at his home. When he woke to find her dead, he panicked and threw her body into the ocean. The truth of the account is suspect, and Burgess has already been released after serving a few years in prison. In fact, Burgess has since been arrested after again using Craigslist to lure women to his home.
4. Katherine Ann Olson Murder
Responding to a Craigslist ad for a babysitter put Katherine Olson in touch with Amy, a mother needing childcare from 10:30 – 5:00. The details were set before Ms. Olson reported to work at a split-level home in Savage. Once there, she was coaxed into an upper area of the home and murdered in cold blood. Michael Anderson, her killer, was a 19 year old man with poor social skills. He killed Ms. Olson with a .357 caliber handgun, before dragging her body down the stairs and tying her up. The motive for the killing is largely unknown, though Anderson received the mandatory life without parole sentence.
5. Philip Markoff Craigslist Killer
The highly publicized saga of the Craigslist Killer involved charges stemming from the death of Julissa Brisman, as well as two additional assaults carried out on women responding to Craigslist ads. The case drew scrutiny for the unlikely perpetrator, who was a pre-med student and seemingly normal chap. As it turns out, Mr. Markoff had a dark side, displaying sexual deviance and other hidden irregularities. But perversion is not thought to be the primary motives for the assaults. Rather, Mr. Markoff appears to have been in dire straights financially, afraid to reveal the situation to his fiancé. Markoff took his own life in 2010, while serving a life sentence in prison.
6. Raped Maid
Michael Delgado called a maid he found on Craigslist to clean his home, but evidence pointed to a different motive for bringing her in. According to the 42-year old maid that came to his home, Delgado was little more than an opportunistic Craigslist rapist. Once there, she claims to have been raped for over an hour, leading to false imprisonment, assault and rape charges against Delgado. Tried at the end of 2012, Mr. Delgado’s jury ended in deadlock, failing to convict or acquit him on the six felony charges he faced. He will be retried on at least some of the charges.
7. Baby For Sale
Paul Marquez probably looked over the ‘for sale’ section for quite awhile before trying to sell a baby on Craigslist. The internet swap meet does not maintain a section for human trafficking. Mr. Marquez posted the ad out of irritation with his newfound girlfriend who mothered the child. According to the complaint, he asked $100 for the infant because it was “on his nerves”. The Craigslist ad was flagged and removed, but the perseverant Marquez reposted the offer. A responder was given the actual mother’s phone number, who then called police to report Marquez. several charges were levied, including child endangerment.

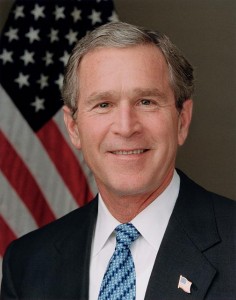
Photo by izzymunchted on Flickr
8. Wine Snob Beating
Seeking the finer things in life is to be admired, but pursuing high-end wine from a discount Craigslist posting carried unanticipated risks for one wine aficionado. When Quy Duc Nguyen showed up to purchase a handful of rare bottles, he got more than he bargained for. Traveling all the way from coast to coast, his arrival was tainted by a beating and robbery that left him with sour grapes.
9. Phone Home Shooting
Jonathan Clements used Craigslist to advertise his need for a new mobile phone. When he set up a meeting with Alexander Lyons, he expected a routine $95 transaction the men agreed upon. Following safe protocols, the meeting was arranged for a public gas station where safety would not be an issue for the men. Lyons pretended to be lost though, and instead was directed to Mr. Clements location, his Aunt’s house. Mr. Lyons was prepared for violence, and soon shot the unsuspecting buyer with a semi-automatic handgun. Mr. Clements died at the hospital a short time later. A life sentence was handed-down to Lyons, and the accomplice who furnished the weapon was also charged with murder.
10. Dao Xiong Auto Ad Killer
Craigslist is widely used for selling cars and motorcycles, so meet-ups are scheduled frequently. St Paul native Youa Ty Lor used the listing service to advertise his Nissan for sale. Unfortunately, a car thief was trolling the wires looking for victims. Mr. Lor agreed to meet Dao Xiong for a test drive, but Xiong reportedly never intended to buy the vehicle. He claims to have been interested only in stealing it, but his plans went awry when Mr. Lor was killed with a forty caliber semi-auto handgun. The murder weapon and telephone records quickly tied Xiong to the crime, leading to his arrest and conviction for the killing. He was sentenced to life in prison without the possibility of parole.
11. John Katehis S&M Killer
When George Weber placed an ad on Craigslist, he was seeking a partner for a sex-related meet-up. The respondent, who later agreed to a sexual encounter for $60, was a twisted Satanist and S&M fetishist. He had a particular preoccupation with knives, which he eventually used to stab Mr. Weber to death. More than 50 stab wounds were present on his body and neck, inflicted by the sixteen year-old killer. Katehis was charged with second-degree murder, as an adult.
12. Long Island Killer
Answering ads for sex is the standard approach for this Craigslist criminal, known as the Long Island Serial Killer. The unidentified perpetrator is though to be responsible for as many as 15 murders in the GilGo Beach area. Over the course of several years, 10 bodies have been recovered from the area, each linked to the killer. While theories abound, it is certain the killer preys on prostitutes and women advertising sex on Craigslist.
13. Boat Buyer Assault
Ronald Kroll used Craigslist for its intended function, placing an ad to sell his boat. After communicating with an interested buyer, Darin Leutbecker, by phone, a test-drive was arranged and the men met at the boat. The 37 year-old Kroll fought back after Leutbecker pulled a gun on him, resulting in shots fired. The men struggled in the boat, before falling into the water, where Kroll eventually remained as his boat was stolen. Kroll was able to inflict some damage of his own, stabbing his attacker with a pocket knife before he fled.
14. Diamond Deal Killers
James Sanders had a diamond ring to sell, so he placed an ad on Craigslist. When four individuals responded for a meeting, Sanders directed them to his home. The Edgewood, WA man was told the ring was to be a Mother’s Day gift, but once inside his home, the group held Sanders and his family captive. As he struggled to protect his children, he was shot dead by the attackers. All four criminals were captured and tried, including 24 year-old Clabon Berniard who received a life sentence.
15. Auto Sale Kidnapping
Selling his BMW was all Alexander Filatov had in mind when he placed an ad on Craigslist. Travis Landry, who responded to the posting had different ideas for Filatov, including a 400+ mile trip in his own trunk. After meeting at Landry’s location, Filatov agreed to a test drive, and the men conducted what appeared to be a legitimate transaction. After accepting payment, Filatov opened the trunk for Landry, who asked to see it. With threats of violence, Landry forced him into the trunk of the BMW, before taking-off on a 450 mile drive. Filatov was not harmed, and his help led police to Landry who was later captured and tried.
16. Work Shirt Robbery
Craigslist does not discriminate among criminals, so it is not surprising that the site aids robberies too. A particularly clever criminal posted an ad for day laborers, instructing them exactly how to dress for the job. Ten men reported to the designated location, dressed as instructed. As they waited for their job assignments, another man emerged in the same outfit. He sprayed an armored guard with an irritant and ran off with a bag of money. The men served as distractions, as the perpetrator jumped into the nearby river. Despite the creative approach, Anthony Curcio was arrested and tried for the robbery.
17. Ellis T. Jones Craigslist Crimes
Ellis Jones played football at San Jose State, where his coach said he was not a disciplinary concern. A different story unfolded as Jones was linked to a robbery plot involving Craigslist. The man used classified ads to lure multiple victims to his location, before Tasing them or threatening them with a gun. The motive was robbery, which did not end well for Jones who was eventually removed from the football team and brought-up on 13 charges of Craigslist wrongdoing.
18. Killer: Alejandro Hernandez Rivera
Prostitution advertising is not limited to women on Craigslist. Alejandro Rivera was a male prostitute advertising regularly online, when he met sixty-six year-old Theodore Neff in 2008. The retired bank employee was a collector of rare flutes, which Rivera targeted to steal. in the end, Rivera strangled Neff to death, before setting his house on fire and taking off with his expensive instruments. Attempting to sell the flutes back to their maker, rivera exposed himself and was arrested for the murder.
19. Baby Killer
After posting an ad on Craigslist for baby clothes, Korena Roberts met Heather Snively. the two became fast friends, sharing what was thought to be mutual pregnancies. The grisly case took a terrible turn when Roberts, who was not pregnant at all, carried out her unseemly plot. the woman killed her friend, beating her to beat with a police baton, before removing the unborn baby from her womb. Both victims died, for which Roberts received a sentence of life in prison with no chance of parole. During the investigation, it was revealed that Roberts had attempted the scheme previously without success.
20. Weyrick Murder
Sarah Weyrick was in dire straits financially, so she placed an ad on Craigslist to make some money. her ad was found in the casual encounters section by a 31 year-old man with grisly intentions. Some time after meeting with Phillip E. Bolden, Weyrick’s body was discovered in a burned-out vehicle. She had been stabbed to death, with multiple knife wounds to her neck. The car she was placed in was set ablaze to conceal the evidence, but the killer was eventually caught.
21. Len Dykstra Craigslist Sex Crimes
Former professional baseball player Len Dykstra has previously been convicted of grand theft auto, resulting from a scam wherein he bought cars with fake paperwork. The sports star turned criminal has had other run-ins with the law too, including a Craigslist crime spree involving sexual misconduct. Dykstra admitted to his crimes, which are essentially the same in each instance. He would call-in Craigslist advertisers for help around his home, only to inform them that the “help” included massaging him. Several women came forward, including one claiming he held her at knifepoint, forcing her to rub him. Dyksta served his sentence for the Craigslist crimes concurrently with his auto theft stint, released in the summer of 2013.
22. iPhone Robbery
When a buyer responded to a Craigslist ad offering a box of iPhones for sale, he got more than he bargained for. According to the complaint, the Seattle man was instructed to meet the seller at a business location where he said he worked. Once there, the buyer got into a car driven by the seller’s associate to complete the deal. Given a box said to contain the phones, he set about getting the 10K in cash out of his trunk. Instead of closing the sale, the seller pulled a gun and demanded the money. The box the man was given contained only scraps of metal and trash.
23. Sister Act
Two Raleigh, North Carolina sisters hatched a robbery plot using Craigslist as their trap. The offer was straightforward – two smartphones for $1100, according to the ad the girls placed. When a Raleigh man showed up to close the deal, things got a little out of hand. Instead of the smartphones, Sherida Quanette Bullock and Acqua Bullock produced a handgun, demanding the cash from the would-be buyer, Ibrahima Diouf. When the man fled instead of giving up the money, the sisters unleashed a hail of bullets in his direction. The Bullocks were each charged with robbery, as was a third woman, Sherie Brooks, who was eventually tied to the crime.
24. Minister Goes Above and Beyond
Hiring a minister to conduct your wedding ceremony shouldn’t put you at risk, but apparently when Craigslist is used to find a pastor, anything can happen. After officiating at their wedding, one Portland minister made-off with the couples’ wedding gifts. Since the pair were remodeling, a majority of their gifts came as Home Depot gift cards. The pastor was easy to locate by tracing the numbers on the cards, which led police to security videos showing the man redeeming them.
25. Girlfriend Revenge
Breaking up is hard to do, but getting even was all that mattered for one Craigslist poster who used the site to seek revenge on his ex. The depraved plan was to post an ad on Craigslist seeking a rape encounter, directing respondents to his ex-girlfriend’s home. Unbelievably, he posted the ad and within a week a man broke-in to the girls home and raped her. The former boyfriend, Jebidiah Stipe, communicated with the rapist even after the ad had been taken down, providing the woman’s home address and additional details about her “fantasy”. Stipe was arrested, as well as the attacker Ty McDowell.
26. Stripper Strike
Hiring strippers for bachelor parties is a tradition to some, but for two would-be strippers it was a one-sided affair. A Huntington Beach man, doing his diligence as the best man, hired two women from a Craigslist ad to strip at a party for the groom. Instead, the ladies collected their $500 fee and then bolted without stripping at all. When the men tried to stop them, they were pepper sprayed and punched in the face. The women escaped with the cash.
27. House for Sale
The deal of the century presented itself to two Oregon women who had a chance to buy a luxury home for pennies on the dollar. The deal they found on Craigslist appeared too good to be true, but the pair, Elizabeth Dorscht and Chandler Cook forked over the down payment anyway. Not surprisingly, the house turned out not to be for sale, and the Craigslist poster disappeared with their money. Lynne Sisto eventually pled guilty to orchestrating the creative scheme.
28. Transgender Assault
Edward Terry Wallace responded to a Craigslist ad placed by three transgender ladies who identified themselves as such in the post. The Chula Vista man reported to the trio’s home and proceeded to rape and beat them. He used a stun gun to control them and robbed each of their cash, before sodomizing at least one of them. For his crimes, Mr. Wallace received a 12 year sentence for sexual battery and robbery of the three.
29. Sex Trafficking Trio
Selling sex is illegal in most places, but prostituting kids is in a whole different class of bad judgment. Nonetheless, three enterprising Craigslist users managed to launch a child prostitution ring on the site. Surprisingly, one of the perpetrators was a woman named Jessica King. Along with her co-conspirators, Jordan Arnold and Christopher Black, King posted pictures of girls in lingerie on Craigslist. The photos lured johns who hired the young girls for sex. All three pled guilty to coercion and enticement of a juvenile into prostitution. Sentences for each defendant were around five years apiece.
30. Rape My Wife, Please
The bonds of holy matrimony didn’t stop an Idaho man from posting ads on Craigslist seeking men to rape his wife. The twisted approach included communicating with the men who responded, eventually steering more than one of them to her home. When one man tried to assault her, the wife grabbed her gun, discharging the weapon. Police responding to the gunfire were brought up to speed about the depraved plot. The husband admitted to his crime and faced the music in a courtroom.
31. No Sex, No Money
A Texas man has been acquitted of killing a woman he met on Craigslist. the man responded to an ad for sex, arranging to pay the woman $150 for the act. He lived up to his part of the bargain, but she took the money without performing her end of the deal. As the two argued over the cash, the woman, Lenora Fargo was shot to death. In a bizarre legal twist, the act was ruled self-defense because the shooter, Ezekiel Gilbert, was trying to recover stolen property at the time the shots were fired.
32. Steven Lewis Kills iPhone Buyer
Lots of Craigslist crimes involve electronics deals gone bad, including the tragic shooting of Mr. Aung Thu Bo. Responding to an ad for an iPhone for sale, Bo and his girlfriend met innocently with Steven Lewis. But Lewis is a convicted felon who ended up taking the unsuspecting Bo’s life. Despite trying to cooperate with the thief, Aung Thu Bo was shot dead in cold blood. Lewis eventually confessed to the crime, claiming the gun went off accidentally.

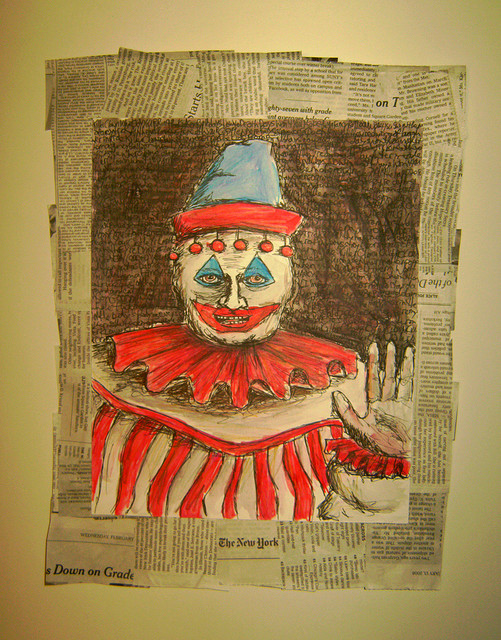
Photo by jason lander group on Flickr
33. Marine Shot Over Necklace
Lt. Col Karl Trenker stood-in for his fiancée who had posted a Craigslist ad to sell a gold necklace. Trenker went to meet a potential buyer in her place, but ran into some trouble. Despite meeting in an open area, the two men posing as buyers decided to steal the necklace and take-off. As he pursued them on foot, Trenker was shot multiple times by one of the men. Jeff Steele fired on Trenker as he chased him, striking him at least three times. Using his military training, the 48 year old Marine plugged the wounds with his fingers, possibly saving his own life.
34. Tiara Pool Murder
Tiara Pool’s killer responded to her Craigslist ad, prompting a meeting between the two. They left the public meeting place to return to Pool’s apartment, where she was brutally murdered. Her killer, David Sparre was 19 years old at the time of the crime, stabbing Poll more than 80 times. The deranged Sparre was sentenced to death for the crime. In a twisted jailhouse letter, Sparre told his ex-girlfriend that he would like to kill again.
35. Daniel Cook ATV Killing
Daniel Cook and his girlfriend were interested in looking at an all-terrain vehicle offered for sale on Craigslist, so they traveled to Philadelphia to meet with the seller. After separating Cook from his girlfriend and another traveling companion, Thomas Coffee robbed and killed him. According to the girl, they were waiting for Cook to rejoin them when two gunshots rang-out. The 23 year-old Willow Grove man was eventually arrested and charged with murder for posing as a Craigslist seller and taking Cook’s life.