Rules of Engagement
On Laws and Home-Brewed Espionage
The laws regarding eavesdropping and spying on family vary on a state-by-state basis and in many cases the legality is not extremely clear. There are cases to support, for example, a husband using GPS software to track his wife’s car without her knowledge or keylogging his home computer to spy on his wife without legal repercussion. Conversely, some have been convicted and jailed for keylogging family computers. Particularly with regard to information gathered with the intent to go to court, it is wise to seek legal counsel before beginning. Be aware that encouraging others to spy on your behalf using illegal methods, whether they are friends or professional investigators, may still leave you legally culpable. Play it safe and educate yourself.
On the subject of digital spying:
Keylogging has become a very popular activity for keeping track of your loved ones and colleagues. Be aware that it is a felony offense to be caught keylogging in the US. It is legal only if an employer has reason to believe an employee may be divulging trade secrets, when a company policy allows for workplace surveillance, if a computer user is clearly notified that their online activities may be monitored, or to track children’s activities online and protect them from predators and other risks. Use against a spouse is legally murky, as seen in the previous examples, and has the potential to land the spy in legal hot water.
Legitimate Cases for Becoming a Spy
There are a multitude of reasons people choose to spy on one another: parents keeping track of suddenly independent teenage children, spouses concerned with infidelity, or perhaps someone requires evidence that a friend has sticky fingers. Perhaps it is simply fun and games – a child play-acting as Bond, James Bond. Whatever the reason, it is important to examine motivations before engaging in spying. In many cases it constitutes a major invasion of privacy as well as being potentially illegal depending on the tools and strategies used, and many would view it as highly unethical. Be sure of what you are doing before you begin. For spouses who may be dealing with infidelity, particularly those with a lot of assets or prenuptial agreements on the line, espionage can be a highly effective means of ensuring smooth divorce proceedings should it become necessary. For parents, it is a surefire way to ensure a child’s online safety. In these cases in particular, the sense of security born from an unalterable truth may outweigh the ethical and moral concerns.
The Value of Social Engineering
Fortunately, there is a tried and true method of gathering information that is wholly legal and requires only a bit of charm and planning. Social engineering has gotten a lot of attention recently for its role in major hacking attempts, but it is equally useful to those seeking information. People are, by and large, inclined to be helpful to someone that does not appear alarming. Take some time to read up on social engineering in depth to make the most of it, here are a few books worth acquiring on the subject.
1) Influence: Science and Practice by Robert B. Cialdini – This book is written in an approachable tone and combines research with experience as a salesperson to instruct its readers in the art of getting a ‘yes’. All about the power of persuasion. Offered on Amazon in paperback for $19.20 or on Kindle for $6.99.
2) Social Engineering: The Art of Human Hacking by Christopher Hadnagy – This book, written by the man who coined the phrase ‘social engineering’, explains through personal experience, real-world examples, and the science that drives it, how social engineering works. It explains how to utilize social engineering and how to minimize risks associated with it. Amazon offers it for $19.12 in paperback or $18.16 on Kindle.
3) What Every BODY is Saying: An Ex-FBI Agent’s Guide to Speed-Reading People by Joe Navarro – Written by a former FBI counterintelligence officer, this book instructs its readers on how to pick up on and translate non-verbal cues as well as how to maximize your own non-verbal cues to subtly influence people. Offered for $13.98 in paperback form on Amazon or $9.99 on Kindle.
4) Introducing NLP: Psychological Skills for Understanding and Influencing People by Joseph O’Conner – This book is well known for its ability to effectively teach the subtle ways in which people can be influenced in the reader’s favor. Written in an accessible style with a clear progression from basics to more challenging concepts, it is considered one of the most definitive NLP texts available. Offered for $10.28 on Amazon.com

On Tactics
Planting Devices
Private Space
– Private places are the most likely to get you into legal trouble, so be aware before you start spying within businesses or private homes. You will need to pick a location that is extremely unlikely to be examined or disturbed by others but that is close enough to main activity centers to pick up useful sound. High shelves, beneath coffee and end tables, behind sofas and chairs pressed against walls.
Public Space
– Placing a listening device in a public location is primarily about determining a place that will usefully return you interesting tidbits of conversation without being drowned out by ambient noise like the sound of traffic, the movement of people, and group conversation. Place microphones, if possible, as far from ambient noise sources as you can be and preferably in enclosed spaces.
On Your Person
– Clothing often muffles the sound incoming, so hiding listening devices on the body can be tricky. You must balance sound quality with visibility. There are listening devices meant to be worn visibly and go unnoticed, meant to resemble buttons or Bluetooth devices. You can also transform your cellphone or similar electronic devices into spy gear and most people will never question it, given the commonality of having such a device at the ready these days.
Inside Things
– Many listening devices are designed to pick up sound through vibrations, so can be safely tucked away within items that have a solid exterior. So long as the device is secured against the internal wall, it can detect and record sound from without. If the device in question can play sound, it will mask any other noise, so items like computers, stereos, cell phones, and TVs are useful to hide devices in but may occasionally interfere as well.
Social Engineering Strategies
5) Dress well – People are much more inclined to be friendly towards someone who looks like they might be important or well connected. Dress the part.
6) Be pleasant – Charm is disarming. Playful flattery of a casual nature, genuine attention, and a warm smile can go a long way towards making another comfortable enough to share information with you.
7) Ask appropriate questions – If you are trying to find out, for example, if your wife is leaving work early it would make sense to ask a company receptionist about her hours so you could schedule a meeting with her. Have a suitable reason for wanting the meeting. Tailor your questions and background to the environment and your needs.
8) Have a reason! – This follows up on the previous idea, but expands it to include accessing private journals or other personal items. If you wish to acquire something in a space you do not belong in, find a good, justifiable reason for you to be rooting around in there. If it is a child, bring them folded clothes to put away. A husband? Dust the shelves in his office. Make it an action that would not be out of place for your behavior. If you never clean, a sudden interest in dusting his things is going to create red flags.

Effective Camouflage
Personal Surveillance
9) If you are intending to actively listen in, there is the chance that someone may encounter you. Dress appropriate to the environment you are in, and be prepared with a good excuse. Despite the title of this section, wearing –actual- camouflage is almost never a good idea.
Remote Surveillance
10) Some of this has already been addressed in ‘Planting Devices’ but be aware that eyes may settle on your device. To increase effectiveness, it is best to conceal the device is possible. Some devices are already meant to appear to be something other than they are – a pen, an innocuous electronic device, a button, or similar. If you are hiding a listening device on a high shelf, consider hiding it within a junk book hollowed out.
Intelligent Preparation
11) Target – Have a clear idea of who you need to speak to, or where you need to be, to obtain the information or items you are after.
12) Goal – Know precisely what you are interested in obtaining. Fishing aimlessly is a sure way to stumble and raise triggers in other people. If you know what you need, you can determine the most likely avenue to acquire that information before you begin speaking. You gain control of the conversation before it begins.
Nifty Gadgetry
Audio & Video Surveillance
13) USB Drive Voice Recorder – This useful little devices looks like a sleek USB stick, but has the added capacity to record up to 45 or 90 minutes of audio with a 15 hours of battery life. It recharges as soon as its insert into a USB port. It does not flash or have any visible notification when it is actively recording and it features incredibly simple operation. $$44.95 for the 4GB (45 minute) option from Pen Recorder Pro.
14) 2.5” HD Dashcam – Designed to affix to your windshield via suction, this camera records clear, quality images even at night. It supports Micro SD cards from 1-32 GB and charges while you are driving with an included cord for your cigarette lighter. It automatically begins recording when you turn it on and includes a date and time stamp (handy if the footage ends up in court proceedings). Just $99.00 from Proof Pronto.
15) Wall Listening Ninja Spy Device – This small tool is designed to be pressed against a solid surface with the intent of picking up sound from the other side. It can ‘hear’ through up to 20cm of thickness and includes a built-in rechargeable battery and an audio jack. It comes with a headset, but you could also conceal the device within an object and connect it to an audio recorder with the right cabling. It costs $49.50 from DX.
16) 500 Meter Spying Transmitter and Receiver Set – This set includes a micro audio spying bug that can be concealed easily and transmits up to 500 meters away. It has adjustable volume and allows for active remote listening with the included receiver or recording on micro SD cards up to 8 GB. It uses a built-in rechargeable battery. Just $90.30 from DX.
17) Cigarette Lighter Hidden Camera Recorder – This faux lighter includes a rechargeable li-ion battery and has the capacity to capture video and picture. It features sound-triggered recording and offers a simple and subtle manual recording mode. It can support MicroSD cards up to 16GB, though they do not include one with the device. The lens is located on the bottom of the lighter. The button that you would normally use to strike the lighter turns it on, and the top removes to access the USB port to upload images to a PC or Mac. Amazon offers it for $99.99, and it is currently on sale for $20.99.
18) Orbiter Electronic Listening Device – This thing isn’t going to win points for stealth, but it is highly effective at detecting audio from up to 300 feet away. It comes with quality headphones and allows for digital recording with a 120 second playback features. It also includes a view finder that can magnify up to 10x.
19) Mini Spy Cam Pen – This executive-style pen in black and gold conceals a HD 3 megapixel camera capable of producing high res color photographs in JPG format or recording video at 1280×960 resolution at 30 FPS. It has a concealed USB 2.0 interface at its end and has driver support for Windows, Linux, and Mac computers. It comes standard with 2 GB of memory and can be upgraded up to 8 GB with a microSD chip. It has a built-in rechargeable lithium ion battery capable of recording up to 100 minutes of video or 6+ hours of photography. Offered for $23.90.
20) Avangard Optics Waterproof Spy Watch – This clever watch features a built-in HD camera recorder, capable of capturing video or stills with 640×480 resolution at 30 FPS. It includes an onboard mic, date and time stamp, with 4GB of built-in NAND flash memory, and connects via USB to a PC to capture gathered data. The watch itself is dust and water resistant and uses a rechargeable lithium battery which lasts for about an hour with a full charge. Priced at $35.00 from B&H.
21) Concealed Camera within a Toyota Car Key – This key records video at 640×480 resolution with 30 FPS and allows storage up to 16GB via MicroSD. It uses a high capacity lithium polymer battery to support roughly one hour of life from a full charge. It connects to a PC with a USB cable for data extraction. Priced at $65.95 from Sears.
22) Spy Clock Camera with Motion Detection – This innocuous camera comes in the form of a sleek and fashionable bedside alarm clock. The concealed HD 2.0 megapixel camera is capable of recording at 1280×960 resolution up to 30FPS. It begins recording when activated via motion detection and can record continuously for up to 2 hours. The AVI files can be transferred directly to a microSD (it comes with a 4GB SD card that can be upgraded for more storage). Costs $48.95 from Newegg.

23) Super High Gain Microphone – This microphone is incredibly lightweight and minuscule, making it easy to conceal nearly anywhere. It weighs less than half an ounce, and the preamp features low noise, powerful high gain and automatic level adjustment with its onboard IC. The output is line level and the device comes with 6 feet of power/audio cables so you can connect it anywhere you need. It needs a 6-15 volts DC battery. Offered for $37.50 from Spy Associates.
24) Coat Hook Hidden Camera – Cleverly hidden, this camera is situated at the top of this hook, ensuring that it will function even while in use. The camera can be activated manually or automatically start when it senses motion. Video is recorded in 1280 x 960 resolution. Available in white or black for $49.95 from Brickhouse Security.
25) Sonic Sleuth Parabolic Microphone – Parabolic microphones help you pick up and isolate sounds at a distance. This particular one is designed for children so the cost is not prohibitive. It can pick up sounds up to 300 feet away and offers a frequency controller to remove unnecessary background noise. It comes with a set of headphones but not the necessary 9-volt battery. Offered by Amazon for $23.21.
26) Uzi Parabolic Microphone – This parabolic microphone also features a monocular capable of viewing up to 8x. The microphone can pick up sounds up to 100 meters (roughly 328 feet) away. It features an integrated chip to record sounds. It includes high quality headphones, but not the necessary 9-volt battery. Offered for $42.95 from Amazon.
27) Sonic Sound Amplifier – While still not necessarily subtle, this sound amplifier is much less obvious to the casual observer than a parabolic microphone. The handheld device can detect sounds up to 300 feet away and can attach via clip to a pocket, belt, and many binoculars. It includes the necessary ‘AAA’ battery and stereo headphones. Offered for $22.95 from Amazon.
28) Smoke Detector Hidden Camera – This pinhole camera is tucked within a nonfunctional smoke detector casing. The camera itself utilizes a CCD (charged coupled device) solid-state imaging device, ensuring top quality image capturing and exceptional reliability. It features auto-white balancing and automatic gain control to provide clear images under normal lighting conditions. It adjusts automatically based on light levels, but will not function well in a dark room. Users will need to acquire power supply and cable separately. Currently on sale at Amazon.com for $34.99.
29) Miniature Wireless Color Camera Set – This set includes a miniature wireless camera with microphone pickup that allows for quality color imaging at a range of 150’ with no obstacles. The camera runs on a 9-volt battery or an AC adapter. The receiving tuner can be fine-tuned to acquire a better picture. The receiver can be set up to record, and can mount on a wall or lay flat for a more permanent set up. Price is just $22.64 via Amazon.
30) Wireless Pan/Tilt/Nightvision Camera with Remote Monitoring – This remote camera can pickup quality images even at night and allows remote access to its pan and tilt functions. It requires a power connection and access to a network and it comes with a power adapter and network cable. Offered for $59.99 from Amazon.
31) Mirror Spy – This security mirror holds a powerful secret camera capable of recording color footage at a 420 TVL resolution. It has a wide angle lens and a coverage range of 82 degrees, ensuring that it can cover an average sized room or hallway. It requires access to a power plug, but does not rely on batteries so once it is installed you can let it run without fear that it will die at a critical moment.
Simple Devices
32) Right Angle Mirrored Lens – This nifty lens attachment will fit any lens with a 58 mm filter thread. It’s simple to install – just screw on and you are ready to use it. It allows you to snap pictures around corners easily without raising attention to yourself. $28.99 from Amazon.com.
33) Telescoping Mirror – These delightful tools generally feature a telescoping handle and flexible neck, allowing you to peak into hard to access places or around the corner without being obtrusive. Generally, they cost a little less than $10. This model from Amazon sells for just $7.29
34) Spy Periscope – While you can make your own simple periscope with a cardboard tube, small inexpensive mirrors, and a hot glue gun, the more dedicated might want to put up the cash for this professional-grade periscope. It makes it easy to see around corners, over, and under all kinds of obstacles and allows magnification up to 5x. Its design ensures that the picture is always displayed right side up regardless of how the periscope itself is set up. SpyVille offers it for $119.99 (on sale for $79.99 at the time of this article).
35) ViewPoint Mirror – Now you too can have eyes in the back of your head, motherhood not required! This handy little mirror is meant to adhere to the inside of your sunglasses and grants users a clear view of what is behind them. Discrete and inexpensive, at just $15.00 from CycleAware.
36) “Safe” Books – A two-piece false book set to conceal your valuables, or a hidden observation device, within. Each book features faux-leather spine and felt lining within the concealed compartments. They are large enough to easily conceal pinhole miniature cameras or listening devices as well as extended media storage or other accessories. The set is currently on sale on Amazon for $29.98.
37) Hide-A-Mic Rocks – Fashioned to resemble a rock, this concealed compartment is designed to secure an extra key, but it can easily be used to conceal a hidden audio recording device designed to pick up sound via vibration through a solid surface. It would not be a challenge to conceal cabling leading to the false rock beneath the ground surface. Currently on sale for $6.02 from Amazon.
38) Make your own false compartment – Any container can easily be provided with a false bottom. There are a number of quick how-to guides online that can walk you through the process. Pick a new item or one that does not get used much. A bedside drawer that is rarely opened or an inexpensive jewelry box. Match the interior when you prepare the false addition. Make sure your measurements are absolutely correct. Create just enough hidden space to conceal your device; the larger the compartment, the more likely it is to be noticed.
39) Concealed pocket clothing – When you are attempting to walk out with potentially incriminating items, or walk in with bugging devices, having concealed pockets can come in handy. Even those with minimal sewing skill can create simple pockets tucked away inside waistbands or jeans. There are also many styles of clothing that come with an abundance of pockets that are easily accessible. Take advantage of functional fashion.
40) Spy Coin (MicroSD concealment) – This realistic looking coin comes in a variety of denominations – A U.S. Nickel, Half Dollar, or Dollar, a British Pound, a 50 cent Euro piece, or an Aussie 20 cent piece. They seal tightly and are completely undetectable from a typical coin and require a special device (included with purchase) to open them once more. Each will fit a microSD card (the U.S. quarter will not, which they also offer). Available for just $18.49 from Amazon.
41) BIC Lighter Secret Stash – This non-functional lighter offers subtle concealment for small items. The size makes it perfect for a microSD card, which is what many spy devices utilize. It looks identical to a typical lighter. Offered for $9.95 via Amazon.
42) Wireless Network Detector Keychain – This simple keychain device detects and displays wireless networks and displays their signal strength via visible LED lights. It comes with batteries. Costs just $5.55 from DX.
Intel Acquisition
43) Wireless Scanning Pen – This silver and purple pen allows users to scan up to 1000 pictures or voice memos up to 1 minute long. It syncs with Evernote and features a storage capacity of 1GB. Offered for $87.73 from DX.
44) Mini Portable Document Scanner – When a pen-sized scanner won’t cut it, this portable scanner can step in. It allows fast scanning of standard sized documents, up to 2 seconds per page with lower resolution. It can scan high resolution images at a slower rate. It stores data on a Micro SD slot and is powered by 2 AA batteries. Costs $54.50 from DX.
45) Spy Remote Control Helicopter – This helicopter can serve as your own personal flying spy. It obviously requires that your target be viewable from an outdoors location. The RC ‘copter can fly for roughly 10 minutes full charged and features a 1G Micro SD card, which can be upgraded. It has a hi-res built-in camera and has a solid state gyroscope for stable control when in use. Users can take snapshots or record video in flight. The RC has an integrated rechargeable LiPo battery that comes included, and the transmitter requires 6 ‘AA’ batteries that are not. It costs $59.95 from Hobby Tron.
46) Spy Mini RC Drone Helicopter – This miniature RC helicopter can fly for 20-30 minutes with a full charge and has a range of 100’ from the transmitter. Multiple bands allow up to 3 RC helicopters to be flown at once. It includes 2 LED search lights, built in gyro for stability, and a mini HD camera to capture and record visual information. The receiver requires ‘AA’ batteries, not included. It costs just $59.98 from Trend Times.
47) Make Your Own Drone – DIY Drones has a ton of information for those interested in crafting their own miniature drones. With the assortment of minuscule audio and visual recording devices on the market and accessible miniaturized RC components, a little technical knowledge and a penchant for DIY is all one needs to create their own spy drone at home. Check out this site for inspiration.
B&E Tools
48) 8 Piece Spring Steel Lock Pick Set – This is a good starter set of quality lockpicking tools. It comes with a double ball lock pick, two different hook lock picks, a snake rake lock pick, a jagged rake lock pick, two different single sided lock picks, and a double ended tension wrench. Each piece is made with black diamond spring steel and have re-enforced handles. Costs $24.95 from Newegg.
49) Super Lock Pick Set – For the more demanding lock-picker, this set includes any style pick you might need, all wrapped up in a faux-leather case. It includes a guide-book to walk you through most lock styles. Costs $96.59 from WayFair Supply.
50) Practical Lock Picking – This guide walks even newbie lock picks through the process of breaking through most lock styles. It includes detailed, full-color diagrams and step by step instructions using a multitude of the most common techniques and tools. Amazon offers this book for $32.72 in paperback and $31.08 on Kindle.
Surveillance Software
51) ISpy Connect – iSpy connects your existing cameras, webcams, microphones and other related equipment into a dynamic surveillance system. Users can set up three types of motion detection and four types of motion processing, with record automated upon detection, or scheduled recording with audio and remote access. It also offers desktop recording and SMS/MMS/emailed alerts. It can be run across multiple computers simultaneously and can even be integrated into iOS devices.
52) I-Can-See-You WebCam Spy Software – This sneaky software runs silently on your PC and allows you to remotely watch it. Whenever your computer goes online, the program sends you an email with an address to connect and watch live. Offered for $29.99.
53) Real Time GPS Tracker App – This application sends an exact location of the mobile device to Google Maps, but only works if the user keeps the program running. Good for tracking children, not good for tracking stealthily. Offered for free for Android devices.
54) GPS Tracking Pro – Another GPS-enabled mobile tracking app, it works best for children as it requires the user to keep the application running on their device. It uses proprietary maps that display local safety points like hospitals and police stations. For any of the GPS phone trackers, you can conceal a locked phone in a vehicle to track its movements more stealthily. This application is free and available for Android devices.
55) Follow Mee – This application turns a smartphone or tablet into a GPS tracker. The app records whatever location the device goes to periodically and sends that data to a secured server. Users can track location data from any browser. It can track multiple devices, establish geo-fences for children, and it runs silently and starts up automatically when the device is turned on. It is designed to stealthily monitor the whereabouts of children, spouses, employees, or stolen devices.

56) Mobistealth – This service offers stealth applications for your computer and mobile device designed to monitor all activities and provide you with a comprehensive report. Cell phone monitoring can allow you to listen in on calls, read text messages, and view videos and pictures sent to and from the phone being monitored. Similarly, the computer program allows you to read emails sent and received, as well as record and listen in on Skype calls, and monitor online chatting. Both can be set up to track GPS coordinates in the case of laptops and mobile phones. Available for Android, iOS, BlackBerry, and Nokia/Symbian phones and Windows and Mac computers.
57) Stealth Genie – This application lets you record and intercept live calls, review call history, redirect or view sent and received SMS messages, view incoming and outgoing emails, and track GPS coordinates. The GPS tracking allows you get updates if it enters ‘restricted areas’ or ‘safe areas’. You are also able to view an assortment of instant message chats, photos, music, videos, and voice recordings as well as view their phone’s calendar and internet activities. Phones can even be bugged to pick up the surroundings and record them or allow you to listen live. Available for nearly any mobile phone and network.
58) XPCspy – A simple to use PC surveillance software. It monitors and reports on all activities on the target computer while running unobtrusively. It allows you to review the log at any time, from any location. Recorded activities including keystrokes, web browsing history, application usage, clipboard history, system activities, emails, and chat conversations. Free trial, $59.95 to purchase after that.
59) IamBigBrother – This keylogging software is designed to run quietly without alerting users and protect against attempts to disable it. It does not show up in the start menu, nor will it be visible in the Task Manager. It can be set up to capture screen shots when certain keywords are typed, it creates a list of all web sites visited, with a title, and the length of the visit. It records everything typed, including incoming and outgoing emails and web chats, and records passwords.
60) SniperSpy7 – This remote computer surveillance software allows users to watch live what is happening on the computer it is installed to. It allows you to browse file systems remotely, view chats, visited websites, keystrokes (in any language), and capture screen shots. You can install it to your computer via email and it is compatible with any firewall. It allows you to remotely download files from the computer, to view and kill active processes, control the mouse, restart or shutdown the computer, and much more. A single 3 month user license costs $39.97.
61) eBlaster7 – Designed to monitor the activities of children and employees, this program is designed to record everything being done on the computer it is installed into, report the activities in an organized fashion to your email as often as you wish, forward to you every email and online conversation, and alert you when certain keywords (pulled from a list you create) are detected, and block web sites or individuals. Costs $99.95.

62) Refog Personal Monitor 7 – Another stealthy program designed to run in the background and monitor the activities of your children. It captures both sides of chats from IM programs, blogs, forums, chatrooms, and more. It can automatically capture screen shots, send alerts when configurable keywords are triggered, and update you via email so you can remotely monitor activities. They offer a free trial version and the cost is $69.95 for the full-featured version.
63) Elite Keylogger Pro – This program claims to be completely invisible when running, able to avoid detection from anti-virus and anti-keylogging software and not show up through any method to computer users. It records keystrokes, including passwords, monitors emails and online chats and allows you to search and analyze online communication, and allows you to capture automatic screen shots. It also offers a deployment installation method, granting you the right to remotely install the software. Monitoring one PC costs $79.
64) Spector Pro – One of the better-known computer surveillance programs, Spector Pro offers a completely undetectable software package capable of recording and analyzing everything any user on a monitored computer does in a format that is easy to review, search, and analyze. You can receive remote access, similar to a remote desktop, and get alerted when certain keywords or sites are accessed. It grants you the control to block websites or access to individuals on the web. You can watch live or use the video-style playback of what they are doing online. Offered for $99.95.
65) PC Pandora 7 – Another stealthy keylogger, PC Pandora’s ability to avoid detection begins with purchase – billing shows up from Click Bank, a common processor for thousands of online shops. When it is installed, it deletes all web browsing history related to PCPandora.com as well. It offers all the typical keylogging functions including web history tracking, silent monitoring, keystroke recording, conversation logs, remote viewing and control, and the ability to block specified websites or individuals online. Costs $69.95 for one year of customer support and access to one computer.
66) WebWatcher 8 – PCMag.com gave WebWatcher a top rating in 2013, and it has gotten great reviews from a number of other sources for good reason. Web Watcher protects PCs, laptops, and mobile devices. You don’t need to have physical access to monitor any device after installation. You can set up your own custom triggers for instant alerts and get near real-time access to everything occurring on your device from any remote location with internet access. It records activities and allows you to review or search through them at your leisure from anywhere. It allows you to view search terms, web history, online conversations, program activity, and record passwords. You can also set up triggered screenshots based on your customized trigger words. Costs $97.00 for Windows or Mac.
67) Spy Agent – A slightly less expensive but very robust keylogger that offers some powerful parental control features, Spy Agent is a good choice for parents or partners wanting to track online activity. Along with monitoring web history, application use, file access and downloads, and online communication, along with triggered screenshot captures and alerts it offers content filtering. This can be used to filter online chats, websites, or applications based on criteria you establish, and notify you and begin automatically logging based on specific keywords, applications, windows, or screenshots. Plus it offers excellent tools for managing the data gathered, including automatically generated reports, top 10 feeds, cross-referencing, filtering, and searching capabilities. It costs $79.95. Not available for the most recent iterations of Windows or Macs.
Just Plain Cool
68) Eviltron – This nifty little device is just a tad bit larger than a US quarter, and includes an embedded rare-earth magnet to make it a snap to hide. The included battery lasts 1 month or more with continuous use. It comes with five scary sounds, and a ‘random’ feature to cycle through them. Use it to draw a person away from a place you need to gain access to. Offered from ThinkGeek Labs via Amazon.com for just $12.95.
69) CheckMate, 5 Minute Infidelity Test Kit – This simple kit makes it easy to collect samples from clothing and linen to locate traces of semen stains. The testing can be done from home and takes minutes to get results. Simply wet the stain, blot the area with a test pad, allow to try, then mix the provided bottle with provided reagents and drop mixture onto the test pad. A positive result turns the sample purple. Costs just $39.99 from Spy Emporium.
Defense Tools
70) Data Encryption Key – To secure sensitive information, use this USB 2.0 device to encrypt and decrypt any file or files you please. It has 128 bit AES hardware protection, and attaches to your keychain so you can always keep it with you. Costs $18.50 from DX.
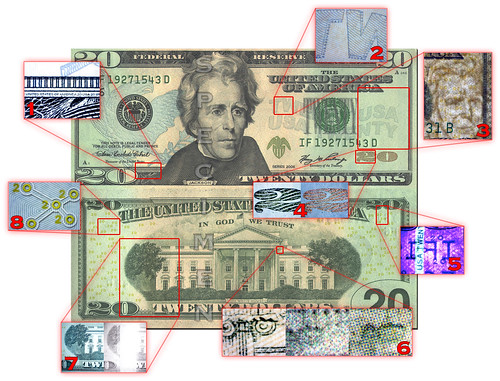
71) Anti-Spy Bug Detector Pen – This pen flashes an LED light whenever it encounters wireless frequencies common to spy cameras and audio recorders. It is not as sensitive as professional level scanners, but is considerably more subtle. It is a functional ball pen and comes with dozens of spare batteries in its included case. The UV LED also works to track blood stains and validate watermarks on documents, bank notes, and money. Costs $13.95 from DX.
72) Anti-Spy Laser Wireless Signal Detector – A professional version of the bug detector pen, this device is capable of pecking up a wide variety of espionage equipment, sometimes as far away as 10 meters. It prevents users from unknowingly being observed or recorded by listening devices, eavesdroppers, or hidden cameras. DX offers it for $44.70.
Required Reading
73) Cyber Spying: Tracking Your Family’s (sometimes) Secret Online Lives – This book is designed to instruct readers in exactly how to spy on someone online. It helpfully covers motivations and the ethics involved, as well as the psychology involved in spying. It gives an introduction to computers and networking basics, teaches readers about online activities and how they can be compromised, and how to prevent being spied on as well. It is designed to help concerned parents and partners check up on online activities. Costs $39.85 for the Amazon paperback edition and $33.56 for the Kindle edition.
74) The Spy’s Guide: Office Espionage – This book is written to help modern day business professional gain the most valuable tools in today’s fast paced world – information. With step-by-step instructions on everything from phone tapping to social engineering strategies, this book helps professionals get ahead. It includes real life stories demonstrating how these techniques have been used successfully by spies in Fortune 500 companies, the CIA, the KGB, and more. Costs $3.38 from Amazon.
75) The Official CIA Manual of Trickery and Deception – Written as a training manual for CIA operatives during the Cold War Era, this manual describes step-by-step instructions on how to gather covert intelligence with sleight of hand and other tricks. Offered for $11.56 from Amazon in paperback.
76) Top Secret: A Handbook of Codes, Ciphers, and Secret Writing – All you need to know on how to create, break, and utilize secret codes and complicated ciphers. Lots of hands on practice, tips for creating your own code-making kit, and tidbits discussing the use of ciphers throughout history. Offered for $6.91 in paperback from Amazon.
77) 101 Spy Gadgets for the Evil Genius – As the title suggests, this is a book with over a hundred projects that you can construct using inexpensive and easy to obtain parts that will allow you to gather intel and conduct surveillance. Projects range from easy to challenging and include a complete list of tools and parts with illustrated guides and step by step instructions. Costs $39.70 in paperback from Amazon, or $14.72 on Kindle.
78) Covert Persuasion: Psychological Tactics and Tricks to Win the Game – Using skills developed with a firm understanding of psychology, linguistics, sales tactics, and human communication strategies, this book teaches you how to become a master of persuasion. Designed especially for sales professionals, but useful for anyone who can make use of a silver-tongue. Offered in paperback for $24.99 from Amazon, and $13.72 from Kindle.

Kid-Friendly Spy Gear
79) Bionic Ear – This simple listening device allows kids to listen through walls, windows and doors. The device works well through glass, sheetrock, and wood. It includes a simple audio earphone. Designed for children aged 8 and up. Priced at $9.39 from Amazon.
80) Amateur Spy Micro Listener Toy – Used to eavesdrop on conversations on the other side of a thin wall or barrier or held at a distance across open space. Includes its necessary LR44 (AG13) battery. Designed for children. Just $2.95 from DX.
81) Spy Net Recording Pen – This recording pen features a secret audio recorder. Stored audio can be accessed via the concealed USB connection. It utilizes 3 ‘button cell’ batteries and unlocks access to the Lie Detector on SpyNetHQ.com. Designed for children 8 and up and offered from Amazon for $17.95.
82) Master Spy Kit – This top secret spy kit comes with an RC car capable of picking up audio and visual signals, a spy pen, two walkie talkies, perimeter motion alarms, and a portable scope. It requires 3 ‘AAA’ batteries that are not included. All of this comes in a hard black case. Toys suitable for ages 6 and up. Offered for $49.99 from Meijer.
83) Top Secret Spy Kit – This professional looking case includes fingerprinting tools, spy glasses, a code book and kit, and more. Meant for ages 8 and up and offered for $39.00 from Land of Nod.
84) RC Spy Tank – This iOS operated RC car features a camera capable of streaming live video of taking photographs. It can travel up to 20 meters without obstacle and up to 10 meters around walls and other obstacles. The car generates is own wireless connection and runs on 6 ‘AA’ batteries which are not included. The controlling app is available free from the iTunes app store. Costs $79.95 from NitroRCX.
85) Long Range Walkie Talkie – Designed for children, these long-range walkie talkies can work up to 2 miles apart. They have a special code button meant to send and receive coded messages, and can also transmit spoken messages. They require 6 ‘AAA’ batteries that are not included. Offered from Amazon for $26.99.
86) Spy Gear Lie Detector Kit – This kit uses a simple finger sensor to pick up the subject’s truthfulness. Indicator lights make note of when the subject is lying. Includes a Lie Detector Handbook. Offered for $12.66 from Amazon.
87) Spy Gear Night Scope – This hi-tech looking night scope allows vision up to 25’ in the dark, includes a spring-activated mechanism to activate a spotlight. It offers a ‘stealth mode’ beam. Offered for $23.99 from Amazon.
88) Multi Voice Changer – A voice changer which offers 8 different voice modifiers and adjustable levers to create a hundreds of modulation options. It requires a 9 volt battery which is not included. Offered for $10.03 from Amazon.
89) Video Recording Watch with Night Vision – This spy watch features a 1.4” full color screen to watch recorded videos and get live playback from the included camera. It includes a rechargeable battery and USB connection and is compatible with both Mac and PCs. It comes preloaded with apps and games, including ‘Spy Detector’ and ‘Lie Detector’ apps from SpyNetHQ. More can be downloaded from SpyNetHQ. Offered from Amazon for $37.69.
90) Stealth Video Recording Glasses – These sleek black-framed spy glasses conceal a camera behind the lenses capable of recording up to 20 minutes of video or capturing over 2,000 pictures. Evidence gathered can be uploaded to PC or Mac with the included USB connection and uploaded to SpyNetHQ.com. Offered from Amazon for $34.34.
91) Color Code Message Kit – This nifty kit includes a decoder filter, message code pad, 4 colored pencils and an instruction manual teaching users how to create and decode color-hidden secret messages. Offered for $5.98 from Amazon.
92) Copper Decoder Ring – This small copper ring contains a basic decoder. The top dial rotates 360 degrees to make it easy to encode or decode a message. Weighs just over an ounch and is only 1-1/2” in diameter. Features geocaching clues. Offered for $14.99 from Amazon.
93) Jefferson Style Cylinder Decoder Wheel – This solid wood decoder wheel allows users to create a message and select their array of encoded letters. High quality and attractive method of sending and receiving secret ciphers. Offered for $23.99 from Amazon.
94) Spy Science Intruder Alarm – This simple device allows kids to create an intruder alert by connecting simple electrical circuits to a door buzzer. Requires two “AA” batteries that are not included. Only $10.49 from Nature Pavilion.
95) EIN-O’s Burglar Alarm Kit – This electronic kit allows children to build their own burglar alarm. Designed for children 7 and up and includes all the parts necessary to make a functional device. Only $7.83 from Newegg.
96) Vanishing Ink Pen – Sometimes you want to leave a message with a built-in self-destruct feature. Exploding messages are hazardous, so the next best thing is vanishing ink. This pen, which appears to be completely normal, features ink that fades after 12 hours. It writes normally on any paper and the ink appears to be typical. Just $4.00 from CrimeScene.
97) Invisible Ink (Homemade) – A good spy knows how to make use of the tools at hand. Invisible ink is a good way to share intel with your fellow spies. Most of us have chemicals at home that we can use to create heat, black light, or chemical reaction based invisible inks. This includes milk, tonic water, laundry detergent diluted, table sugar solution, vinegar, and acidic fruit juices. About.com has a great article on homemade invisible ink that can get you started.
98) Permanent Invisible Ink Marking System – Of course, if you want to ensure the longevity of your invisible message and be sure you have a way to review it later, you may want to purchase this pen. The invisible ink is permanent and waterproof, ensuring its longevity on non-porous surfaces. It includes a UV light so you can check the message after it has been written. Costs $11.99 from Whatever Works.
99) Invisible Ink Pen & UV Light – This less expensive pen allows users to write secret messages that can be revealed with the included UV light. It’s only 5 inches long, so easy to conceal, and priced at just $1.49 from Lazerpoint it is inexpensive enough to stock up on them.
100) CSI: Fingerprinting Analysis Kit – This kit, available from Toys-R-Us for just $17.99, contains everything a budding investigator needs to examine evidence. It includes tools to gather and analyze fingerprints and other data. It is targeted towards forensic analysis but could be adapted for the budding spy.
101) Spy Gear Evidence Kit – Made specifically for young spies, this kit comes in a professional-looking black hardcase and contains a UV blacklight, a functional 30x microscope, a 10-piece fingerprint kid, and an LED flashlight. Priced at $20.38 from Amazon.











 EMBED THIS INFOGRAPHIC ON YOUR SITE
EMBED THIS INFOGRAPHIC ON YOUR SITE