Author Archives: Heather
Data management and security are an important part in the daily lives of most people these days. A lack of knowledge on how to keep your data under control and organized can mean your business suffers in productivity or a hacker halfway across the world can loot your bank accounts. Luckily, the number of mostly altruistic experts who want to share their wisdom on data management and security is impressively large, and many of these experts and the companies who employ them maintain blogs that can be easily browsed to keep yourself abreast on the current state of the IT and InfoSec world. This list contains links and quick glimpses into thirty of the best offerings on the web. Blogs are divided into data management blogs, security blogs, and those with content that bridges the gap between the two.

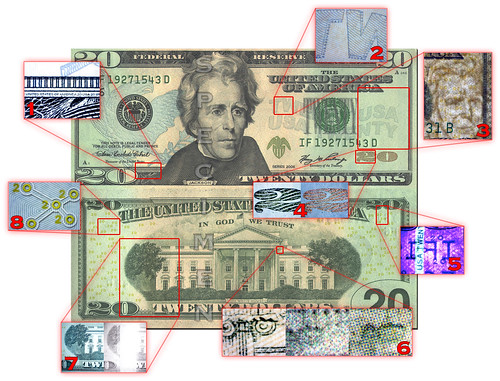
Data Security by Charlie Collis
Well-Rounded Blogs
- Rational Survivability– Originality can make a sometimes-dry topic like technology more bearable for the masses. Rational Survivability makes no apologies that it is a personal blog that will do whatever it wants, whenever it wants to do it. Almost every post can pull a laugh from you while still imparting some knowledge. The posting rate seems to be on the decline over the past few months, but you can still expect a new post per month. The blog has been in existence since 2006, so it is likely going to stick around for a while. Throw it in your monthly blog checklist and you won’t regret it. Must Read: An Ode to Glasses, a somewhat clever and definitely hilarious poetic tribute to Google Glasses.
- Rud.is – This blog is a bit of a hard one to place. The subjects range from data security to shiny graphs to random IT subjects, and occasionally it even goes off the grid into something completely different. It does not have the best update rate, and the varying content makes it hard to suggest that you put it on your frequent reading list. That said, it is worth giving a quick look at some of the articles to determine if the blog is something that you might like. Must Read: Security Hobos, a discussion on truly small business owners who are blissfully ignorant that they are creating terrible security problems for their customers.
- From the Trenches – There is no substitute for experience, but reading about someone else’s experiences comes in at a close second. From the Trenches is a mix of stories from the owning company, Solera, and related posts on data security and management problems that have had an impact in the real world. The blog is fairly heavy on advertising posts for Solera, but considering that it is all but declared directly in the blog’s mission statement that this will happen, we can forgive it this time. Must Read: Topera, the Sneaky IPv6 Port Scanner, an article that provides an overview of one malicious tool and that serves as a good example of the sort of content you will find here.
- Attachmate: Data in Motion – The moment where any sort of information is at the highest risk of falling into the wrong hands is when that information is in transit. Attachmate provides solutions for information security for electronic devices during this vulnerable stage, and their blog provides useful tidbits of information on how to properly secure file transfers. As you would expect from the more pointed focus of the company, the blog is narrow in scope. Unfortunately, the blog does not take advantage of this to provide lengthy or detailed information, instead opting for more general updates on file transfer news and technologies once or twice a month. Even though we think this blog could be great with just a bit more effort, it is still a decent one to have on your monthly checking schedule. Must Read: User-driven File Transfers and You, a brief commentary on why email should not be used as a file transfer system.
- Verizon Terremark: Enterprise Cloud Blog – Terremark is a division of Verizon that delivers Cloud and enterprise level solutions to medium and large businesses. Their blog is a mixture of company news and informative articles on the Cloud, big data, and security. One of their more frequent topics is “News to Know,” which contains small excerpts and links to other articles. It isn’t a terrible blog, but with about 40% of the content being company advertising and re-posts, it isn’t a great one either. A good amount of information and updates coming every day or so are its main redeeming qualities. Must Read: Encryption Solutions in the Cloud, a post on the encryption options that work best for Cloud technologies.

Weir Data – Photo by Acoustic Dimensions
Data Management Blogs
- Obsessive-Compulsive Data Quality Blog – Focused on providing his readers with a very thorough review of the importance of data quality, management, and security, author Jim Harris creates well-written and informative posts on his blog. Posts range from analyzing the costs and issues that stem from poor quality management, new techniques to utilize and protect data, vendor reviews and news presented in a neutral way, tools and resources, and much more. An excellent source for anyone involved in the data chain Must Read: Magic Elephants, Data Physics, and Invisible Gorillas – glancing over the excitement surrounding Hadoop (the Magic Elephant), its potential use to predict customer data kept close to the chest (Data Physic), and a warning about getting too far ahead with data changes (the Invisible Gorilla).
- Data Quality Pro – Data Quality Pro is a community managed website built with the vision of collecting the insights and ideas of professionals in the world of data quality. The blog itself has a decent color scheme, but the layout and navigation can be more than a pain until you get the feel for it, and it will still likely irk you even then. They make up for the haphazard design with four to five posts a month that are unique and insightful for the world of data management and analysis. Must Read: How to Create a Data Quality Firewall and Data Quality SLA, a useful set of tips and advice for less tech savvy companies looking to hire a data quality company.
- Mike 2.0 – Mike 2.0 is an open source information management solution that features community blog project with useful posts from experienced and intelligent members of the data management field. Some of the contributing bloggers appear frequently on other sites or maintain blogs of their own. The layout makes it easy to navigate through the content, but the color scheme is a boring and somewhat irritating choice of primarily white with light blue backgrounds. As with other community blogs, the higher number of contributing authors means the blog is updated with original content fairly frequently. In addition to the blog, you can find a discussion board to communicate with other readers and the contributors. Must Read: The Increasing Meaninglessness of the Data-Metadata Distinction, a short but thought-provoking post about how much information is really contained within metadata and what it can tell someone about the contents.
- Information Management – Information Management, despite the rather bland name, is a massive resource on just about any topic on which you could tack the words “data” or “information.” If you want to know about data encryption, data security, big data, data quality, data analytics, data storage, the Cloud and data, data on the network, or anything else, you can find it here. The layout is incredibly busy and can seem overwhelming, but they do fairly well considering the amount of material that is stored on the site. There are multiple blogs within the site, links to educational resources, a webinar repository, and more. This is a resource that will serve you above and beyond the fields of encryption and security, but it definitely fits in with them as well. Must Read: After a Data Breach It’s Often Business As Usual, a chastising look at companies who do not take data breaches to heart and implement better data management procedures.
- Midsize Insider – As the name suggests, Midsize Insider is a blog site and article repository geared towards imparting information management know-how to small and medium business owners, managers, and IT staff. With dozens of contributors and staff members, content on the site is always fresh and is released at least daily. The navigation is a bit jumbled and the main pages are a bit overwhelming with information from Twitter, infographics, trending articles, and article lists. Once you get into the articles, things clean up and do not interfere with reading. Midsize Insider is essentially a normal blog on steroids: a bit harder to keep up with, but it packs more punch. Must Read: PRISM and Encrypted Data Benefits, an article on the recent NSA domestic surveillance fiasco and the importance encryption plays in keeping sensitive data safe when anyone – even the government – may be watching.
- The Data Roundtable – The Roundtable is a moderated but open posting ground for experts on data management in all of its forms, including subjects like data analytics, management, encryption, and general security. The blog has a marked informal tone, with topics for the posts having some silly sounding titles like “On Lawnmowers and Data Management.” The levity belies the depth of information, experience, and the ease at which many of the contributors impart their knowledge to readers. The layout is sleek and crisp, and the content is updated on an almost daily basis. This is one of those blogs to keep on the top of your list. Must Read: What’s the Meta with Your Data?, a suave title for an intelligent discussion on the importance of metadata.
Juniper – InfoSec 2013 – Photo by David
Security Blogs
- Schneier on Security – Operating since October of 2004, blogger Bruce Schneier has developed a strong following and respect from other bloggers interested in cryptography and related studies. The layout of his blog is very reminiscent of the late ’04 web, but contains a wealth of well-written information relating to everything from computer crime, homeland security, privacy, malware, policy issues, and much more. Frequently updated and easy to navigate, Schneier on Security serves as an excellent resource for those looking to dig up gems from this blog’s archives. The blogger himself is an acclaimed expert in security technology, with recognition for his numerous academic and other published essays, dozen published books, assorted fellowships, media and Congressional appearances, all of which got him dubbed a ‘security guru’ by The Economist. Must Read: Intelligence Analysis and the Connect-the-Dots Metaphor,
- Security Bloggers Network – Not a blog in its own right, but rather a collecting house of related blogs, this is a great resource for those looking to take a peek at what is new and exciting in the security blogosphere. They host a blogger hall of fame and annual security blogger award as well as an open feed of new posts to help users find quality blogs of interest. Worth checking out if you are a blogger or an avid consumer of such. Must Read: Security Blogger Awards, for a round-up of regularly updated and well-written security blogs.
- CSO– Expert advice on security from a range of experts. Posts cater to organizations and businesses concerned with protecting data. Regularly updated and well-written, but unfortunately sponsored by intrusive ads that require you to click-through them to get to the content. This site also offers webcasts, white papers, and an emailed newsletter so readers never miss interesting news. Must Read: Are you sure you’re really in control of your servers? This article discusses some of the threats to even owned servers.
- Cognitive Dissidents – This security blog features a gorgeous site design with no nonsense commentary on security issues from the perspective of self-declared zombie killer, philosopher, and security strategist. While not frequently or regularly updated, the blog offers a fresh perspective and is well worth a gander. Must Read: A Replaceability Continuum, an examination of the question, ‘How replaceable is an asset type.’
- Uncommon Sense Security – Blogger Jack Daniel, an Information Security Curmudgeon, writes with a great deal of experience on the InfoSec industry with content that is unsponsored and uncensored. Expect to find no-nonsense posts on a whole range of related topics and the occasional helping of acerbic wit to raise a chuckle. Regularly updated since June of 2007, this site is clean and straightforward to navigate. Must Read: Managing employees and expectations, for a rant on how to retain quality InfoSec personnel.
- Andy Ellis > Protecting a Better Internet – Primarily targeting the clientele of the information security industry, this blog is an excellent resource to get a handle on trends, methods, terminology, related news, and events. Regularly updated since May of 2006, Andy Ellis has been providing readers with information that is incredibly easy to parse no matter a reader’s experience level. His focus is on internet security and steps that can be taken to tighten up sites to prevent leaks, scams, and other threads. Must Read: Leveling up Security Awareness, for a solid article addressing one of the biggest weaknesses in security protocol – the human element.
- Threatpost – The Kaspersky-owned Threatpost blog is one of those selections that make you do a double-take when you find the tucked-away reference to the parent company. From all appearances, you would believe that Threatpost is run by InfoSec enthusiasts who do their job for the love of it. The update rate is astounding, and checking the blog every day for content is the bare minimum unless you want to fall drastically behind. Topics center on security related news such as malware, cryptography, and hacking. We are confident enough that the great design and implementation of the blog will speak better for itself than we can, so stop by Threatpost as soon as you can. Must Read: Royal Baby Spam Campaign Leads to Black-Hole Infected Site, because it is one article about the royal baby that won’t leave your brain melting out of your ears.
- LiquidMatrix – This refreshing InfoSec blog screams “educated and edgy” from the moment you pull up the home page. The layout is slick and beautiful while facilitating easy reading and the glimpsing of information. You will find ten or more posts per month that touch on InfoSec news from around the world. They are accompanied by the podcast which releases episodes every couple of weeks and are amusingly numbered in hexadecimal. In fact, the podcast could be considered the major draw of the site, and you will greatly miss out on the value of LiquidMatrix if you skip over the episodes. Two of the sections we like the most – a list of default passwords on almost 1000 devices and their critical security advisory page – do not get the navigational focus they deserve, so make sure to check the small content box for links to them. Must Read: What to Do If Your iPhone Gets Stolen, a handy read for the millions of users of the Apple smartphone.
- Krebs on Security – Krebs’ blog is one of the most popular and active personal sites in the InfoSec blogosphere. The author, Brian Krebs, has years of experience in professional writing, most notably a long stint with the Washington Post. Like many people today, he began in another field and gradually gained interest in the ins and outs of the IT world. His blog contains frequent updates with a focus towards malware, exploit kits, hacking news, and security in general. Most of the articles go above and beyond the brief articles found on other sites, and many of his technical reviews of malware and exploits can prove to be lifesavers. The popularity of Krebs is well-deserved due to the quality and frequency of its postings, and it should easily find a spot in most people’s roundup of InfoSec related readings. Must Read: Web Badness Knows No Bounds, because while you may think that avoiding sites that scream danger will protect you, browsing online always presents some level of risk.
- The Falcon’s View– The Falcon’s View has all the qualities we like in a personal blog: most of the posts are original content authored by the owner, it keeps a good update frequency despite having quality content only created by a single author, and the writer is knowledgeable and legible while seeming approachable. The author is an employee at Gartner and a contributor to their blog, but he still cross-posts his own content to his personal blog. The only real negative that can really be attached to the blog is the background colors are not the best, but that does not detract from the enjoyable and unique content. Must Read: Arguing Against the Absurd, an article where Ben shows the proper way to comment and discuss on a post from another blog or source.

- TaoSecurity – A growing number of malicious attacks on networks throughout the world are originating from one place: China. TaoSecurity brings all the information related to the threat of Chinese hackers into one spot. The author of TaoSecurity is Richard Betjlich, an experienced InfoSec specialist and author. The blog has been in existence since 2003, pointing to the alertness and awareness of the situation that noted the oncoming problem long before it became the subject of national attention. Due to the narrow scope of the blog, the posting frequency is understandably low and sits at about two per month. Must Read: President Obama Is Right On US-China Hacking, a post with commentary and a link to President Obama discussing some of the ongoing issues with Chinese hackers.
- Securosis – With a no-nonsense approach to InfoSec research and education, Securosis skips past the marketing and posturing that other company blogs include so well that we could not even include it in the InfoSec company blog section. Posts tend to come up once or twice a day, and they are typically unique articles with a purpose rather than reposts, links, or brief commentaries. If you finish the daily offerings and want more, the research library contains what they consider their key posts on a variety of security subjects. The library is not updated frequently, but it serves adequately as a secondary resource and a good place for those just getting started. We also love the coloring on the blog since the off-white post backgrounds makes extended reading easier on the eyes. Must Read: Endpoint Security Buyer’s Guide: Buying Considerations, a post every business owner should read before they sign up for security services.
- Network Security Podcast – Sometimes, the medium your information is delivered in can play a big impact on how likely you are to go through it and the level of enjoyment you get out of it. This is where podcasts come into play, as they function essentially like audio blogs. The Network Security Podcast features a lively crew of InfoSec specialists who banter and discuss the most newsworthy topics in network security. While many blogs offer multiple viewpoints, it is difficult to get the same depth of discussion and debate that you do from having multiple people conversing. A new podcast is released around every two weeks, and they make for a great bit of listening while working on other tasks. Must Listen: Their June 18th, 2013 podcast that touches on everything but the immensely covered Snowden case.
- Network Security Blog – This blog is maintained by a sole contributor named Martin McKeay, a friendly fellow who works as a “Security Evangelist” in California and is also a regular figure in the podcast noted above. The posting schedule is a bit haphazard, but he does throw up somewhere near five notes a month on average. The articles range from analysis of network security news, tips and advice on proper security methods, and links and commentary to other useful resources. There is nothing noteworthy about the design and scheme of the blog, but there is nothing wrong with using what works. The blog has been in existence since 2003, providing over 1000 posts to rummage through if you want to get caught up. Must Read: Rage Against the Machine, a collection of informative links related to the NSA PRISM project.
- HiSoftware: Shooting from the Hip – HiSoftware is an information security company that provides a “Governance, Risk Management and Compliance (GRC)” platform to companies and organizations that want to keep their data safe. The blog for the company focuses on the issues of data management and security, most frequently featuring topics like data breaches, problem technologies, security standards compliance, and news related to data security. The look and feel of the blog has some nice touches, but it remains fairly standard overall. Posting occurs at a fairly nice rate with updates coming in every three or four days. Must Read: This article on the threat SharePoint can pose for data leaks is illuminating even while it highlights the role HiSoftware’s service can play in preventing the same thing from happening to your business.
- ThreatVision Labs – ThreatVision is the blog for Solera Networks, an information security company that focuses on providing solutions for Big Data. The content focuses mostly on reports of malware and other security threats that can wreak havoc on your data, providing higher level overviews that give enough of the technical side of things to point you in the right direction if you want to learn. Articles are posted roughly four times a month. The blog’s design is simplistic and effective, garnering no complaints while not really astounding anyone. You should also hop over to ThreatVision’s sister blog that we mentioned above, From the Trenches, which contains more anecdotal looks at information security in the field. Must Read: Five Cybercrime Trends Likely to Continue in 2013, since it always pays to be up to date on the network attacks you are most likely to experience.
- Tenable: Network Security Blog – Tenable’s blog is one of the best company blogs on the list when it comes to the amount of content delivered. They offer a regular podcasts, webcasts, frequent posts, tutorials, white papers, RSS feeds, and newsletters. The blog does push the products of the company fairly hard, but it is relatively tolerable due to the sheer amount of other content. The content is updated almost every day, but you can probably get enough out of the blog by spending a few minutes on it every two or three days. Must Read: Prove You’re Watching 100% of Your Network, a post which points out that even the companies who keep an eye on their networks may not be doing so well enough.
- Hacker Academy Blog – The Hacker Academy adheres to the “know your enemy” strategy that has proven itself time and time again. They provide a look at security from the view of those who do their best to circumvent it, and you cannot protect against things you do not know about. The blog is updated roughly every month in a haphazard schedule, but the posts in the blog are less important than the library of information available on the site. The layout is basic with a soft grey background that makes it much easier on the eyes. They offer training modules on a variety of security topics and frequently hold webinars. The information is presented a clear and concise fashion that makes it accessible for newcomers and experts alike. Must Read: Hacking Fundamentals, one of their training modules and a good look at the basics of the hacker mindset and toolkit.
- VeraCode Blog – Veracode is a company that offers Security as a Service (SaaS) through their Cloud-based Application Risk Management Platform. They focus on security testing for applications, which is why their blog splits itself between general security news and tips for programmers on how to secure their applications. The layout of the blog is fairly bland, featuring a scheme that is mostly just a white background. Updates come along every two or three days, and they do a good job of keeping obvious plugs for the company to the bare minimum. The blog is minimally useful for security programming tips with a pointed focus towards security news. Must Read: 4 Things You Should Know Before Writing Another Line of Code, a quick list of useful tips to keep in mind for security while programming.