Author Archives: Alexa
Realistically, anyone with access to data dumps from fiber-optic lines belonging to American telecom carriers will eventually be able to read your communications. However, it’s entirely possible to make it much more difficult for anyone to be able to pinpoint and decipher your movements online. When you can hide a message so that no one even suspects it exists, that is most secure, and if you can use a less traveled path of connection it also helps hide your tracks.Some people have figured out smart ways to stay invisible, but connected.
But if you’re like most of us and still using the public telecom system for browsing and e-mail, you’ll want to try out many of these 172 privacy tools to anonymize your web presence, encrypt your data, and erase your tracks.
- SSL – Secure Sockets Layer (SSL) protocol is a layer of software that operates between HTTP (internet protocol) and TCP (protocol for moving internet data from point to point), and it preserves security in internet transmissions by using RSA encryption.

Socket wrench, universal joint and sockets. Courtesy of Kae, 9 December 2008
- NoScript – NoScript is an extension for Mozilla-based browsers that uses a whitelist to decide which sites can use plugins like JavaScript, Java, and Flash. It also lets you control cross-site scripting and clickjacking.
- HTTPS Everywhere – HTTPS Everywhere is an extension that works with either Firefox or Chrome, and the “S” means your HTTP connection has been secured by encrypting data that passes between your computer and other network locations.
- CyberGhost – CyberGhost advertises itself as a free utility permitting anonymous web surfing, and it also encrypts all your transmissions, which is perfect protection for any public location.
- LastPass – LastPass is a secure password manager that gives you one master password to access its interface. LastPass will then use your stored credentials to log you into any other site you request.
- LongURL – LongURL is a web interface that expands short URLs so you can see where a link is taking you. It supports a number of formats like TinyURL and bit.ly.
- Trusteer Rapport – Trusteer Rapport’s endpoint security software performs ongoing data collection to power its behavioral algorithms in order to block phishing attacks and installations of Man-in-the-Browser malware.
- Two-step verification – Two-factor or two-step authentication adds security to your login by requiring two pieces of virtual identification from you. Google’s version asks for a password plus an on-the-spot phone code.
- VirusTotal – VirusTotal is a free online utility that lets you scan dubious-looking files (maximum size is 64 MB) and URLs. VirusTotal records scan results and makes that dataset available for searches.
- Tor – Tor keeps your browsing anonymous by using onion routing, a network of virtual tunnels which screens your location and activity within the network to make sure no one eavesdropping on the network knows who’s communicating.
Barbus tor or Tor tor (Hamilton, 1822) from the Bhavani river. Courtesy of Henry Sullivan Thomas, The Rod in India, 1897
- Duckduckgo – Duckduckgo is a search engine that keeps your searches private by refusing to collect or share any information about you and what you search for on the web.
- StartPage – StartPage is another private search engine that functions as a go-between, removing any data on you from your web queries before sending them to Google and relaying Google’s answers back to you.
- Smart Referer – A Firefox add-on called Smart Referer lets your browse anonymously by removing any information about where you came from when you use a link to move from one site to another.
- Bitdefender QuickScan – Bitdefender QuickScan is an online virus scanner to detect any malware currently running on your device. Don’t ever permit this kind of scan from an unknown agent, but you can trust Bitdefender.
- HTTPS – HTTPS is a secure network communication protocol that adds HTTP programming, for hypertext capability, to SSL/TLS programming, for security. Security includes encryption and certificates used to identify the sender and receiver of transmitted data.
- Sophos Virus Removal Tool – Sophos Virus Removal Tool is a free download that looks for viruses, spyware, rootkits, and the Conficker worm. It checks not only files but also both user and kernel memory .
- Microsoft Safety Scanner – There’s no charge to download the Microsoft Safety Scanner, and its 10-day expiration date means it’s intended for one-time use, to address a specific infection.
- VPN – A VPN, or virtual private network, provides private communications between computers using the public telecom system. This is achieved using tunneling, and it’s a cheap substitute for a secure private line.
- Dropbox – Dropbox is a free cloud service with security features (SSL and AES-256 bit encryption) that lets you save and share files. When you save a file on Dropbox, Dropbox in turn saves that file on all your devices.

VR pillar box in George Street, Oxford, England. Courtesy of Motacilla, 11 October 2011
- FTPS – FTPS (secure FTP) is a new version of the old FTP (file transfer protocol), updated to add security. It’s a file transfer utility that moves data over an encrypted channel.
- TLS – TLS (transport layer security) is a secure communications protocol intended to supplant the older SSL, using symmetric cryptography for privacy and an MAC data integrity check.
- CuteFTP – CuteFTP is an FTP program that consolidates all older versions, including Pro, and offers a new mobile service called TappIn that gives you instant secure FTP connections among all devices on your network.
- ShareFile – ShareFile is a Citrix product, a top-end secure file transfer package with a high file size limit (10 GB). Data storage meets SSAE 16 guidelines.
- Core FTP LE – There’s no cost to download Core FTP LE, a file transfer utility that lets you choose among five different security protocols. It has no nags, ads, or registration.
- IronKey(tm) – IronKey(tm) secure flash drives have a Cryptochip feature to ensure drive encryption and password requirement. Certified to meet Federal Information Processing Standards (FIPS) 140-2 Level 3 standard.
- Keystroke Interference – Keystroke Interference thwarts keylogging software, which records your keystrokes, by adding random characters to all your input. It includes AI to learn and camouflage your personal style of typing.
- HouseCall – HouseCall from Trend Micro is a free online scanner that targets viruses, Trojans, worms, harmful browser plugins, and malware. Now has added ability to specify files and folders.
- Check Point GO – When you plug in a Check Point GO secure flash drive, it creates a protected environment so you can work from someone else’s PC without risking your data. Includes VPN client.
- Linux – Linux the operating system boasts two strong security advantages. Different levels of access shield sensitive data, and varied distribution details mean one virus design can’t affect all Linux users simultaneously.
- Wontok SafeCentral – Wontok SafeCentral is a packaged solution for businesses that ensures safety by preventing applications from interacting with anything other than Trusted Security Extensions, thus foiling malware.
- SecureAnywhere(tm) Complete – SecureAnywhere(tm) Complete gives you continual anti-virus protection for all types of devices, including browser warnings. It even protects you while you’re signed into Facebook and Twitter.
- Firesheep – Firesheep is an extension for Firefox that shows users which of their HTTP connections (e.g. to Facebook or Twitter) inadvertently reveal their account information. In public wireless tests, Firesheep listed all insecure accounts of users in the vicinity.
- HTML Purifier – HTML Purifier is a HTML filter library that uses a whitelist to block cross-site scripting (XSS). It’s a handy open-source tool for anyone who has to produce secure HTML pages.

Tata Swach is a low-cost water purifier that works on the principles of nanotechnology. Courtesy of Globalfunky, 27 May 2010
- Proxy server – Proxy servers are the core of anonymization on the web. Any direct communication between your computer and another network location may compromise your data, but if you communicate only with a proxy that proxy will relay your requests to the outside world and bring the responses back to you.
- Windows Defender – Windows Defender was originally designed to combat spyware, but has been expanded in scope to cover all malware. Your PC may not have shipped with Defender turned on, so make sure to check its status.
- Spybot – Search & Destroy(r) – Spybot – Search & Destroy(r) is a perennial classic in spyware detection, and even though it’s added anti-virus protection it’s still free. Use the Immunize function to strengthen your browsing defenses.
- MailWasher – MailWasher blocks spam and the viruses it can contain by letting you preview e-mail safely. You can examine what’s on your remote e-mail server and download only the mail you know to be no threat, deleting the rest.
- Active Spam Killer – Active Spam Killer (ASK) is for Unix and Linux installations. It filters out spam by sending a confirmation request when it receives e-mail from an unknown source, then whitelists the senders that reply.
- McAfee SpamKiller 4.0 – McAfee SpamKiller 4.0 is a standalone spam filter that lets you filter and review e-mail that’s on your remote server before you download it, so you don’t have to risk bringing questionable mail onto your own computer.
- Wireshark – Wireshark is a network security tool that allows you to analyze your network traffic by capturing and displaying packets of data in a comprehensible format as they pass through your network.
- Snort – Snort detects and prevents network intrusions. It’s free, it’s open source, and it can be used as a packet analyzer, packet logger, and threat defense system.
- SpiderOak – SpiderOak secure cloud storage provides an online home for data stored on all kinds of devices. It’s instantly accessible, completely private, and includes synchronization for file-sharing.
- TrueCrypt – TrueCrypt provides free disk encryption software for Windows, Mac, and Linux. You can encrypt any of the following: virtual disk, partition, flash drive, or OS partition.
- Cain & Abel – The best way to determine password strength is to test it using a password cracker, and Cain & Abel provides that service for any Microsoft OS.
- John the Ripper – John the Ripper was designed as a fast password cracker targeted at identifying weak Unix passwords, but you can also use it to test passwords for other operating systems like Windows and DOS.
Image: A Suspicious Character, collection: Illustrated London News, With the Vigilance Committee in the East End, October 13, 1888. Courtesy of Illustrated London News, artist unknown, uploaded by Jack1956
- fgdump – fgdump is an updated version of an old favorite password tester called pwdump, and it specializes in Windows-resident NTLM and LanMan passwords. Requires administrator access.
- KeyScrambler – KeyScrambler’s different versions support anti-keylogging measures in between 32 and 200 browsers, depending on how much you pay. Premium also protects your keystrokes in cloud services Dropbox, Google Drive, and Sky Drive.
- Tcpdump and libpcap – Tcpdump and libpcap together form a perennially loved and used network traffic analysis package, in which tcpdump captures packets as a command line utility and libpcap is a complementary C/C++ library for that traffic capture.
- Kismet – If you need a program that performs packet analysis for wireless networks, try Kismet– it can detect other networks and tell you whether anyone’s breaking into your network.
- OpenSSH – If you ever experiment with building your own internet communications system rather than using a third-party browser and e-mail application, you’ll need a basic encryption tool like OpenSSH to shield all your data traffic.
- PuTTY – PuTTY is a perfect example of a simple internet transmission program that goes through telnet and uses SSH for security. What PuTTY does– open a secure channel through which your computer can access another directly– is how the peer-to-peer internet used to work, and the privacy advantage is obvious.
- SSH – SSH, or Secure Shell protocol, provides guidelines for secure and private login and exchange of information over the insecure public telecom system. It replaces the old telnet protocol.
- Ettercap – Ettercap lets you stress-test your own network by launching man-in-the-middle attacks in which it intercepts and alters communications. Don’t miss the countermeasures section to help you use what Ettercap teaches you.
- IP identifiers ping, dig, and traceroute – Any time you need to know the identity of an IP making unsolicited contact with your computer, remember these three basic tools that can help you track down the offender: ping, dig, and traceroute.
- Paros – Not sure whether one of your web applications has been secured? Test it with Paros, a Java-based proxy that reveals vulnerabilities to frequently used attacks like cross-site scripting.

The Paros seafront in Greece. Courtesy of Dimorsitanos, August 2009, cropped by Beyond My Ken 20 September 2010
- Fake AP – If your wireless network has suffered unauthorized activity, or has shown up on a public detection map without your consent, you can camouflage your location by erecting a screen of short-lived access points with Fake AP. For defense purposes only, please.
- Google Hacking for Penetration Testers – Google Hacking for Penetration Testers: This remarkable paper on revealing your system’s vulnerabilities by using Google queries will show you how easily an attacker can view website pages you thought were securely hidden.
- Procmail Sanitizer – Procmail Sanitizer is a behavioral e-mail security tool. Instead of checking for viruses, it lets you choose a set of rules such as “attachments cannot access the registry or execute code” limiting what your e-mail and its attachments are permitted to do on your system.
- Sender Policy Framework and Sender ID – Sender Policy Framework (SPF) and Sender ID are similar methods of validating IP addresses permitted to send mail from your domain name, used as authentication that distinguish between legitimate mail generated by you and spam.
- Tails – Tails is a portable OS that lives on a DVD or flash drive. It includes a number of built-in applications like a browser and an e-mail client, and it’s designed so you can use any computer to surf anonymously.
- S/MIME – Secure/Multipurpose Internet Mail Extensions (S/MIME) protocol secures your e-mail by laying out rules on how to encrypt mail, ensure message integrity, and authenticate senders using digital signatures.
- SonicWALL(tm) – SonicWALL(tm) Email Security is a strong, scalable business package by Dell that includes controls for each end user mail account, so you can tailor user permissions individually.
- Barracuda Email Security Service – Barracuda Email Security Service (BESS) offers secure cloud e-mail to businesses that want to host their own e-mail but pay a third party to provide spam filtering and malware protection.
- Norton AntiVirus – Norton AntiVirus is a gray eminence in the world of paid malware protection, and while its 2014 product is double the price of the original, the software is still reliable.
- Enigmail – Enigmail is a plugin for Thunderbird and Seamonkey that adds OpenPGP protection to your e-mail by way of both encryption and digital signature authentication. Requires the free GNU Privacy Guard.
- Cloud Security Readiness Tool – Microsoft’s Cloud Security Readiness Tool requires you to answer a set of questions about your current IT setup to generate a report in response, aimed at exploring how moving to the cloud can help secure your business data.
- Trend Micro SecureCloud 1.1 – Trend Micro SecureCloud 1.1, for users of Trend Micro’s Beta Portal, provides encryption for your cloud storage. Service includes your choice of AES encryption type.
- CipherCloud for Google Gmail – CipherCloud protects your all business data traveling through Gmail by providing a secure reverse-proxy interface and a mail transfer agent that adds encryption for inbound mail.
- Porticor Virtual Private Data – Porticor Virtual Private Data is a cloud system that uses encryption to guarantee data security that will meet regulatory requirements for safeguarding sensitive customer information.
- CloudPassage Halo – CloudPassage Halo offers secured cloud storage geared at businesses that must comply with regulatory requirements for protecting their data. Halo lets you automate your security policy while adjusting the parameters of your storage at will.
- The Bat! – The Bat! comes in several flavors and offers e-mail encryption plus secure authentication. SecureBat! is now The Bat! Professional, and its addition of hardware tokens produces very strong security.
- The Anonymizer – As you gathered from the “legacy content” notice, the original Anonymizer was one of the first anonymous surfing services appealing specifically to users who objected to being tracked. You can pay for today’s Anonymizer, or treasure the memory.
- Proxymate – If you’ve always wanted to access websites that are forbidden to U.S. surfers, try a proxy based in another country. You can gamble on British sites by routing your traffic through Proxymate.
- Onion routing – Onion routing, like so much of web technology, originated with the U.S. military as a DARPA project. It was devised as a means of hiding location information, and that’s the same function it performs today in anonymous surfing.
- HidemyAss with PPTP – HideMyAss is an anonymous surfing service that employs Point-to-Point Tunneling Protocol (PPTP) to give you an encrypted VPN connection, and supplies clear instructions on how to set up a PPTP connection with a dialer.
- Guardster – Guardster has several different proxy products aimed at privacy, including a free online proxy service and two subscription services, an encrypted SSL proxy and a secure SSH tunnel proxy using the SOCKS, or Socket Secure, protocol.
- iPhantom – The iPhantom proxy service keeps you anonymous during your contact with other web locations, and for further privacy does not store any of the identifying information describing your contact with the iPhantom server.
- IP Hider – AllAnonymity’s IP Hider inserts a proxy server to relay your web requests, meaning the IP visible to marketing trackers belongs to that proxy rather than your computer.
- AVG – AVG Free is one of the anti-virus programs that offered enough quality to break the grip of paid services like Norton. Those companies used to sell AV software with free updates, and when they converted to a package-plus-subscription model they inadvertently sparked the boom in AV freeware.
- avast! Free Antivirus – avast! Free Antivirus is a justly favored product, delivering sturdy detection and removal at no cost for a full quarter of a century. Happy Birthday, avast! Many people team avast! with AVG because what little one might miss, the other usually catches.

Capture of the Pirate, Blackbeard, 1718 depicting the battle between Blackbeard the Pirate and Lieutenant Maynard in Ocracoke Bay. Courtesy of http://www.neatorama.com/2007/10/22/pirate-lore-7-myths-and-trrrrruths-about-pirates/,
by American painter Jean Leon Gerome Ferris, 1920 - Panda Cloud Antivirus – Panda Cloud Antivirus protects your stored data from viruses and spyware. It uses behavioral analysis to recognize and stop new malware and includes community firewall protection.
- Malwarebytes Anti-Malware Free – Malwarebytes Anti-Malware Free specializes in removing all kinds of malware, but is particularly effective against worms, trojans, rootkits, rogues, dialers, and spyware. You can automate updates and scanning.
- Ad-Aware Free Antivirus+ – Ad-Aware Free Antivirus+ adds anti-virus capability to its classic spyware defenses. It now prevents malware from being written to disk in an inadvertent download, and runs unknown executables in a safe sandbox environment.
- Comodo Antivirus – Comodo Antivirus offers a free edition that keeps viruses and other malware of all your devices. It employs cloud-based scanning to find questionable hidden files.
- Comodo SSL Certificates – Comodo SSL Certificates are your way of guaranteeing your web customers safe contact with your site, using SSL to shield customers’ personal financial information. Comodo has been in the SSL certificate business since 1998 and provides good client support.
- Emsisoft Emergency Kit – If you have ever been confronted with an infected PC and encountered difficulty controlling its behavior, you’ll welcome the Emsisoft Emergency Kit. It downloads onto a flash drive, and you can plug in the drive to scan your PC for viruses.
- Avira Free Antivirus – Avira Free Antivirus provides not only broad-spectrum malware protection but also adds two extra features by way of a toolbar to block tracking in your browser and rate the security levels of sites you visit.
- Rohos Mini Drive – Rohos Mini Drive lets you password-protect your flash storage with a hidden, encrypted partition. The Portable option lets you use a similar secret partition on any PC.
- Kryptelite – Kryptelite is freeware that provides basic encryption and decryption ability, and if you upgrade to other Kryptel products you can get more advanced features like encrypted backups and scripted encryption.
- Pismo File Mount Audit Package – Pismo File Mount Audit Package lets you mount several file types as virtual folders, including encrypted, password-protected private folders which let you conceal data on your drive.
- Free File Camouflage – Free File Camouflage is a steganography tool that lets you hide your messages inside a .jpeg image file. The goal of steganography is not only to encrypt but to let your messages escape notice altogether.

Mgr Patrick Le Gal, évêque aux Armées françaises. Courtesy of Mangouste35, 06/08/2008
- Ad-Aware is no longer safe as of testing September 9, 2013 – Hearts all round the world broke when Lavasoft, producer of once beloved antispyware stalwart Ad-Aware, inserted unwanted toolbars and even a browser hijack into free Ad-Aware downloads. You can avoid lengthy and painful removals by avoiding Ad-Aware altogether.
- CTI Text Encryption – CTI Text Encryption is a free text encryption tool with support for multiple languages, including those read from right to left. Recommended for creating strong passwords.
- AxCrypt – AxCrypt is an open source file encryption project designed for Windows, and it includes the following capabilities: password protection, encryption in the right-click menu, double-click to work with encrypted files, and automatic re-encryption after editing.
- Anti Tracks Free Edition – Anti Tracks Free Edition removes all traces of your computer activities from your hard drive, including browsing history, temporary files, installation logs, and other telltale signs of your passage.
- ToolWiz Bsafe – ToolWiz BSafe offers file encryption with simple features that produce advanced results. Its ability to mount an encrypted folder as a virtual drive is described as “opening the safe,” because the only time that hidden data is accessible is while you’re working on it.
- BCTextEncoder – BCTextEncoder presents its free e-mail encryption program as a way to avoid the embarrassment of sending an e-mail to the wrong recipient. Uses public key and password-dependent encryption.
- Anonymize.Net – Anonymize.Net provides anonymous web browsing using a VPN (virtual private network), with one offshore proxy in Panama and a continental proxy in Canada. Use their handy WHOIS page to see your own IP revealed, and then check the difference when you view the page by proxy.
- the Cloak – the Cloak functions as an online proxy service, and has published a clear and helpful explanation of how a proxy can help you refrain from displaying your private information to web trackers.
- Internet Anonym – Steganos has a line of anonymity/privacy products, perhaps the best of which is Internet Anonym. Internet Anonym protects your IP even when you have to use public WiFi , letting you choose details of false information displayed by your browser.
- Idzap – IDzap offers three ways to protect your privacy on the internet. You can choose IDzap Free Anonymous Browsing Service, you can pay for a fully featured version called IDsecure Anonymous Browsing Service, and you can add encrypted e-mail with IDseal Secure Email Service.
- CryptoHeaven – CryptoHeaven provides a suite of secure encrypted e-mail services, encrypting not only the messages themselves but also the hosting and online storage features. CryptoHeaven’s goal is leaving no weak points in its data security.
The Great Last Judgement, Peter Paul Rubens. Courtesy of L’Alte Pinakothek di Monaco
- Snoopblocker – Snoopblocker is a free online web proxy service that lets you enter a URL and browse anonymously, with several encryption options neatly arranged in checkboxes.
- Z1 SecureMail Gateway – Z1 SecureMail Gateway is billed as a “virtual mail room” that handles all encryption, decryption, and digital signature authentication for your e-mail. You can tailor individual security policies by using the console.
- Hushmail – Hushmail is an encrypted e-mail service based in Canada, it promises not to display any third party ads, and it gives you a free trial period. The Personal option is expensive, but service is reliable.
- Lawdex Secure Document Exchange – Lawdex Secure Document Exchange (SDX) is designed for businesses that need to keep client records in strict confidence, particularly law firms, medical practices, and financial services companies.
- Mutemail – Mutemail bases its secure e-mail service offshore, and if you already use a secure client (Mutemail specifies Secure Bat! and Thunderbird as examples), you can use that program through Mutemail’s SSL interface.
- NeoMailbox – NeoMailbox, hosted in Switzerland, offers secure e-mail plus anonymous browsing with IP concealment, SSL connections, and even disposable e-mail addresses if you prefer to communicate with that level of anonymity.
- ShareMeNot – Whenever you see embedded buttons from companies like Facebook or Google, those companies are tracking you. ShareMeNot disables the tracking until you deliberately click one of the buttons in order to share.
- Greasemonkey – Greasemonkey is unquestionably the most helpful of the Firefox extensions because it lets you add scripts to Firefox to achieve any goal you like, including user security and anonymity. It will also accept .js files that you create.
- Don’t Facebook – Don’t Facebook, EVER, if you wish to keep your private information out of the public eye. That being said, if you must Facebook at least keep up with your privacy settings, and to do that you have to stay apprised of the latest policy updates.
- Ghostery – Ghostery is not only effective in blocking web trackers, it’s a lot of fun to use. You will be shocked at the number of active trackers you find, and you’ll enjoy killing them off. Firefox addon.
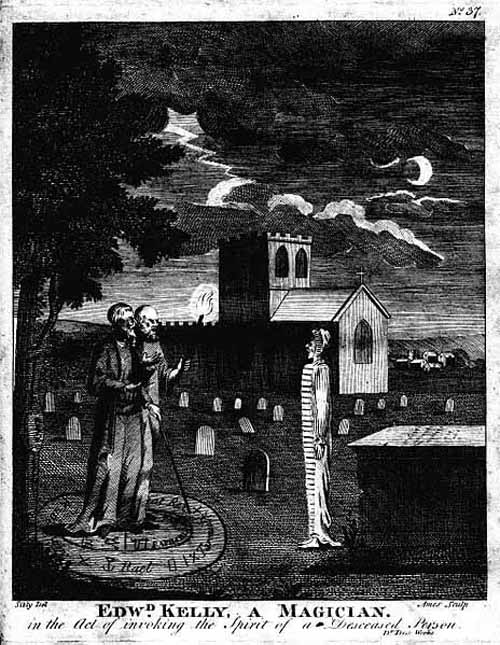
Edwd Kelly, a Magician. in the Act of invoking the Spirit of a Deceased Person. Courtesy of fromoldbooks.org, taken from Astrology, A New and Complete Illustration of the Occult Sciences by Ebenezer Sibly, M.D. F.R.H.S., Embellished with Curious Copper-Plates, London, 1806. Engraved by Ames of Bristol, original drawing by Sibly.
- DoNotTrackMe – DoNotTrackPlus has grown up to be DoNotTrackMe, but it still gives you a free and simple way to block more than 600 online trackers from following you around the web. Firefox addon.
- TrashMail.net – TrashMail.net creates junk e-mail addresses that forward mail to you, then terminate automatically after catching a certain amount of mail. You can sign up with insecure sites without risking your preferred address. Firefox addon.
- Ultimate Privacy – Ultimate Privacy offers a complete privacy and anonymity service that lets you perform all your online tasks safely. Includes browsing by proxy, disposable e-mail addresses, and PC eraser. In business since 1997.
- SpamAvert – SpamAvert offers an interesting disposable e-mail service online. You choose a word to serve as a one-time junk mail address, then come to SpamAvert to pick up your mail.
- Adblock Plus – Adblock Plus was born in 2006 as a free Firefox addon, and it’s been blocking annoying ads all over the world ever since. You choose which ads to block based on filter lists.
- CsFire – CsFire guards against cross-site scripting, whether the problem is a Cross-Site Request Forgery attack or simply an attempt to track your browsing habits. Firefox addon, now available for Chrome.
- SmartScreen Filter – SmartScreen Filter uses blacklists of phishing sites, malware sites, and malicious files to vet your browsing and downloads, displaying warnings when appropriate. Built into Internet Explorer 8 and above.
- PrivacyChoice – PrivacyChoice helps you stay private on the web with free online scanning for your website or app. Software offerings include Privacyfix to manage your privacy settings on sites like Facebook and Google.
- Boss Key – Boss Key is a child’s trick that might save your job by letting you hide that browser or game with a simple keystroke, including cutting the sound and changing screen resolution if necessary.
- Certificate Patrol – Certificate Patrol is a Firefox addon that inspects certificates and certificate hierarchies to make sure a site is safe to visit. Inspections are also performed for individual parts of each page.
- Telex – Telex is the old communications system that uses automated teleprinters (think Western Union in the mid-20th century). Today, web customers in censorship zones use secret Telex requests hidden in HTTPS connections to escape the zone and surf freely.

Telex machine T100 manufactured by Siemens. A sign inside said ‘T.grpl.82, T100; nüral F5230.’ Courtesy of Flominator, 11 February 2005
- Long URL Please – Long URL Please expands short links within a page while truncating the new long link to keep the page formatted properly. You can set options for how you’d like your links to change, and Long URL Please works with most types of short links. Firefox addon.
- Disconnect – Disconnect is a tracking blocker that actively keeps up with new trackers as they are added. There’s a small toolbar button showing overall status and a dropdown to give you more detail.
- ScriptNo – ScriptNo is a Chrome extension that tells you about scripts that have been, or could be, blocked on every page. Uses whitelists and blacklists to help you set preferences.
- Ccleaner – Ccleaner from Piriform cleans up your Windows system, making it harder to track you online with cookies and sweeping out temporary files, download history, and Autocomplete settings.
- HOSTS file – A Windows HOSTS file is a list of host names that match to IP addresses, and a specially edited HOSTS file can make your browser skip downloads of web flotsam like cookies and banner ads. You can download such a file from MVPS HOSTS.
- Pidgin – Another secure messaging client that uses OTR is Pidgin, which is free and open source. You can use the Pidgin interface to manage your other IM applications.
- Don’t Google – Don’t Google, EVER, because Google has no respect whatsoever for your web privacy, and makes no bones about invading it in order to monetize your personal data. A quote from Google’s recent court filing: “a person has no legitimate expectation of privacy in information he voluntarily turns over to third parties.” Ouch!
- Gibberbot – Gibberbot uses existing messaging applications like Google Chat and Facebook Chat to offer an unlimited free communication option that’s encrypted using the OTR (Off-The-Record) standard.
- GnuPG – GnuPG, or GNU Privacy Guard, is the Gnu project’s version of OpenPGP, as laid out in the 2007 specifications called RFC 4880. It’s a command line tool you can insert in code for your other applications.

Gnu. Photo taken at Kliprivier Nature Reserve, Johannesburg. Courtesy of derekkeats, Flickr: IMG_4955_facebook, 9 May 2009
- GSMK CryptoPhone 500 – The GSMK CryptoPhone 500 gives you strong encryption plus full source code access so you can verify your level of protection. Includes voice encryption and secure messaging.
- Speak Freely – Speak Freely is a VoIP program for Windows, meaning you can use it to call another PC and have a voice conversation over any network that uses TCP/IP. Special instructions for encryption are available.
- Zfone – Zfone is a VoIP program that lets you use the internet to make encrypted phone calls. It uses the new ZRTP protocol produced by the same engineer who designed PGP.
- Mil Shield – Mil Shield not only erases but also shreds your computer’s history files, removing not only browsing history and Autocomplete information but also index.dat files and Flash cookies.
- Private Eye – Private Eye is a handy utility that lets you see and edit what’s in your protected storage area, which holds data about what you’ve been doing on your computer (including browsing).
- Sookasa – Sookasa is an encryption program that works with Dropbox, creating its own folder in your Dropbox directory and automatically encrypting any files placed therein. Designed for businesses who want to remain data-compliant in the cloud.
- PC-Encrypt – PC-Encrypt has several encryption products. A-Lock encrypts e-mails, PC-Encrypt encrypts your files and folders, and a utility called PC-Docmail even sends encrypted files directly from your desktop to recipients.
- Mixmaster – The Mixmaster remailer protocol involves sending packets of equal size in rearranged order to make them less traceable, which explains the name. Mixmaster protects against packet analysis and provides anonymity.

This is a hand-held electric beater (also known as a hand-held electric mixer). Courtesy of Donovan Govan, taken using a Canon PowerShot G3, 24 April 2005
- Pretty Good Privacy – Pretty Good Privacy (PGP) is an an email encryption program originally distributed by MIT, and when it was released in 1991 it spread around the world, enraging the American government. Today PGP is the guiding principle of most secure e-mail communication.
- PirateBrowser – PirateBrowser bundles the Tor client with a proxy-enhanced version of Firefox and adds some special configuration to produce a means of eluding the web censors in those countries so afflicted.
- PGPdisk – PGPdisk is a utility that creates encrypted disk partitions, and it is now distributed as part of PGPfreeware 6.0.2i. Later versions beginning with PGPdisk 6.5 can only be found in paid programs, but the plan is to keep older PGPdisk free.
- Symantec Drive Encryption – Symantec Drive Encryption provides full disk encryption that includes the following types of files: user, swap, system, and hidden. Works on not only computers but also removable media.
- Check Point Full Disk Encryption Software Blade – Check Point Full Disk Encryption Software Blade (yes, it’s a long name) protects everything on your hard drive, including personal data, OS files, and temporary files.
- Neo’s SafeKeys – Neo’s SafeKeys lets you use a virtual keyboard displayed on your monitor to input sensitive data like personal information and passwords. That means there’s no way to record your keystrokes, because no keystrokes are used.
- SecureDoc – SecureDoc makes sure your data stays secure with full disk encryption, multi-factor authentication instead of single passwords, encryption of removable media, and basic file and folder encryption.
- File Shredder – File Shredder is a free application that thwarts software designed to retrieve deleted files from Windows computers by overwriting the deleted files several times, making it impossible to recover them.
- AbsoluteShield Track Eraser – AbsoluteShield Track Eraser is a comprehensive data removal system capable of erasing all of these: browser cache, history, cookies, typed URLs, autocomplete information, and saved passwords.
- Burn 2.5 – Burn 2.5 overwrites deleted Mac files using the same overwriting process recommended for shredding Windows files. Burn is a free utility and recommended for use with encryption software Enigma.
- E3 Security Kit – E3 Security Kit is the privacy subset of the Windows tool package Extreme Power Tools (XPT). It’s built around the ShredPerfect+ utility, described as a long, dull, highly effective process that’s guaranteed to destroy your files completely.
- Eraser – Eraser is a free application that not only overwrites individual files but also ensures any extra copies are removed by erasing any free space on the disk.

Standard pink erasers, made by Sanford. Courtesy of Evan-Amos, 09-28-98
- Evidence Neutralizer – Evidence Neutralizer cleans traces of your activities off your PC, making it difficult to follow you by using temporary files, Autocomplete information, browsing history, and even index.dat files.
- SDelete – SDelete is a data overwriting tool written by a Microsoft employee that you can download at no charge and use anywhere you’d normally use a command-line utility.
- Privacy History Eraser – Privacy History Eraser removes all your internet history, including sites you visit, recently used files, downloads, cookies, and temporary files. It looks for items left behind by Windows programs like Internet Explorer and Windows Media Player.
- Pwgen – Pwgen, or Password Generator, creates random, secure passwords that are deliberately easy for you to memorize, because you can pronounce them. The utility was written by a Linux open source coder.
- AutonomyCentral – AutonomyCentral is an e-mail client secured with both RSA public key and 256 AES encryption, and it works with the privacy-oriented Vaultlet Mail application. You can send and receive messages from your flash drive.
- Random Password Generator – Random Password Generator is an online utility that produces a nonsense word you can pronounce which ends with a number. There’s also a version for iPhone and iPod.
- Sectéra(r) vIPer(tm) Universal Secure Phone – If you’re looking for extra strength in phone security, the Sectéra(r) vIPer(tm) Universal Secure Phone by General Dynamics can provide privacy that’s suited to classified information. The phone is recommended for government use.
- ZoneAlarm Free Firewall – ZoneAlarm Free Firewall gives you unobtrusive protection against hackers and malware at no cost, and it’s designed to work well with other antivirus programs. Includes privacy toolbar.

Wheelock MT-24-LSM fire alarm horn. Photographed by Ben Schumin on November 23, 2002. Courtesy of Ben Schumin, edited by ZooFari, edit April 17, 09
- Tonga Remailer – The Cypherpunks are encryption-oriented privacy strategists, and one of their efforts is the Tonga Remailer. The Tonga Remailer is based in the country of Tonga, and it’s an anonymous remailer that uses the classic Mixmaster protocol.
- Firewall Free – Comodo’s Firewall Free gives you basic firewall protection, including anti-virus capability, warnings about particular files, and automatic updates if desired. There’s also a free version of a similar Mobile and Tablet Security program for your other devices.
- CNET is no longer a trustworthy download source – There’s bad news from the free download front: CNET is no longer a trustworthy download source. It’s developed a bad habit of forcing unwanted utilities like junk toolbars and adware on downloaders, and its use should be avoided.
- Online Armor – Online Armor Free gives you basic firewall protection at no cost, including spyware defenses, browser safety, and meaningful messages. Added features include HOSTS file checking, control over start-up programs, and keylogger blocking.
- AntiLogger Free – Zemana AntiLogger Free instantly encrypts all your keystrokes so keyloggers are presented with unreadable, secured data. It works for every application you use rather than just your browser.
- SpyShelter Personal Free – SpyShelter Personal Free baffles keyloggers while protecting your system and defeating capture of any data from your screen or clipboard. There’s also a paid Premium option.
- MyPrivateLine – MyPrivateLine provides disposable phone numbers that you can give out to anyone without worrying about revealing your identity or location. The disposable number forwards to one of your real numbers.

Western Electric Company Princess phones. Green one is rotary dial, has hardwired handset cord, and dated November, 1973. Yellow one is Touch Tone dial, has a modular handset cord, and dated June, 1984. Courtesy of User:KansasCity, 15:30 24 February 2006
- KeePass – KeePass is a password manager, free and open source, that lets you keep all your passwords in a single database secured with a master key file.
- 1Password – The 1Password generator not only creates strong passwords for you but also stores them securely, recalling them into your browser at your command. Available for Windows, Mac, iOS, and Android.
- Encrypting File System – Did you know Windows has its own file encryption utility? It’s called Encrypting File System (EFS), and unfortunately it’s available only in Professional, Ultimate, and Enterprise editions. It exists in the file right-click menu’s Properties, and it’s very easy to use.
- Vormetric Data Security Manager – Vormetric Data Security Manager is a piece of hardware that manages security for your server installations of Vormetric Encryption Expert Agents. It generates and distributes keys, and it can also provide encryption.
- Vasco Online Application Security – Vasco describes itself as “the authentication company,” and its active and passive authentication services will secure your online applications that handle sensitive financial and health-related data.
